Series Editor
Dr. Thomas A. Johnsonpresently serves as Dean of the School of Public Safety and Professional Studies and also Dean and Director of the University of New Haven–California Campus. Dr. Johnson received his undergraduate education at Michigan State University and his graduate education at the University of California–Berkeley.
Dean Johnson founded the Center for Cybercrime and Forensic Computer Investigation and serves as Director of the Forensic Computer Investigation Graduate program. Additionally, Dean Johnson was responsible for developing the online program in Information Protection and Security at the University of New Haven. Dean Johnson also designed and developed the National Security and Public Safety Graduate Degree Program, which is being offered both at the Connecticut Campus and at Sandia National Laboratory in Livermore, California.
Currently, Dean Johnson serves as a member of the FBI Infraguard program and also is a member of the Electronic Crime Task Force, New York Field Office, U.S. Secret Service. The United States Attorney General appointed Dean Johnson a member of the Information Technology Working Group, and he served as Chair of the Task Force Group on Combating High Technology Crime for the National Institute of Justice.Dean Johnson was also appointed an advisor to the Judicial Council of California on the Court Technology Task Force by the California Supreme Court.
Dean Johnson has published two books and 13 referred articles; he holds copyrights on four software programs; and, in October 2000, his chapter “Infrastructure Warriors: A Threat to the U.S. Homeland by Organized Crime” was published by the Strategic Studies Institute of the U.S. Army War College. In addition to lecturing at the U.S. Army War College, CarlisleBarracks, he has also lectured at the Federal Law Enforcement Training Center and numerous universities.
Dean Johnson has appeared in both state and U.S. federal courts as an expert witness and was a member of the Select Ad Hoc Presidential Investigative Committee and consultant to the American Academy of Forensic Sciences in the case of Sirhan B. Sirhan, regarding evaluation of ballistics and physical evidence concerning the assassination of United States Senator, Robert F.
Kennedy.
23
| Computer Crime and the Electronic Crime Scene | 1 |
|---|---|

THOMAS A. JOHNSON
In the mid-1960s our nation experienced its first series of criminal activity in which a computer was used as an instrument to perpetrate an economic crime. In his book,Fighting Computer Crime, Donn B. Parker reports that in 1966 the first federally prosecuted case of a computer crime involved a consultant working under contract with a Minneapolis bank to program and maintain its computer system. This case was unique: Theindividual was prosecuted for embezzlement of bank funds because he changed the checking account program in the bank’s computer so that it would not identify and automatically notify bank officials of overdraft charges in his personal checking account (Parker 1997, 8).
By 1973, the largest recorded and prosecuted computer crime had occurred in Los Angeles and resulted in the destruction of the Equity Funding Insurance Company, with a loss of $2 billion. Twenty-two executives and two auditors were convicted for creating 64,000 fake people, insuring them and then selling those policies to re-insurers (Parker 1997, 65). Law enforcement agencies were not prepared for the use of sophisticated computers in these economic criminal acts. In fact, the first federalagencies to participate in these criminal investigations were the Internal Revenue Service (IRS) Criminal Investigation Division, the U.S. Secret Service, and the Federal Bureau of Investigation (FBI). When one examined the training provided by those agencies to their personnel, there was little or no instruction offered in terms of computers and their use in criminal acts. Agents who were assigned to these cases had to develop and refine their individual skills to address the challenges they were encountering in the field.
1
I.Introduction and Historical Developments
The IRS Criminal Investigation Division (IRS-CID) was the first federal investigative agency to contract with a university to develop and refine the skills of an elite group of special agents to confront this new and emerging trend in criminal activity. Michael Anderson and Robert Kelso were among the first group of IRS-CID agents to receive this training in computers and to play a leadership role within their agency. Another pioneer in this newly emerging field was Howard Schmidt, who would eventually be called on to serve as vice chairman of the President’s Critical Infrastructure Group. Howard’s career began in a small municipal police agency in Arizona, and he eventually served in several important federal agencies where, through his vision and encouragement, he created programs to train other law enforcement personnel at the local, state, and federal levels of government. Howard Schmidt’s skills did not go unnoticed by the corporate community, and, as computer crime was increasing, the corporate community turned to him and a select few others for assistance in combating these new developments in corporate criminal activity.
Universities also were not prepared for how computers might be used in the commission of criminal activity. As a result, law enforcement had to rely on the insights of such leaders as Howard Schmidt and Michael Anderson, who were both instrumental in developing training seminars for their colleagues. Indeed, the very beginning efforts of organizations such as the International Association of Crime Investigative Specialists (IACIS), and the High Technology Criminal Investigation Association (HTCIA) were specifically developed to offer training, instruction, and sharing of information in this important area. Eventually the HTCIA began developing chapters in various states and regions and, to this day, is one of the most respected organizations for professional, in-service training of law enforcement officials interested in computers and their role in criminal activity.
If law enforcement agencies were ill-prepared for the challenges they would confront in computer crime and economic crime cases, our prosecutorial agencies were even less prepared for this growing criminal activity. One only has to examine the absolute dearth of statutory law in each of our states to realize that we were not prepared to prosecute these cases. Once again, our nation had to rely ona small cadre of people who saw these challenges and played a most formidable role in providing their colleagues with the training in this area. Leaders such as Kevin Manson, Tony Whitledge, Ken Rosenblatt, Gail Thackeray, and Abigail Abraham provided enormous assistance not only to their colleagues but also to state legislators in the framing of new statutory law to address this new criminal activity.
In the early 1980s the SEARCH Group, Inc., under the leadership of Steve Kolodney (and afterwards, Gary Cooper), perceived a need for training law enforcement managers in Information Management Systems. Fortunately, the SEARCH Group also had two outstanding pioneers in the field of training police officers in computers — Fred Cotton and Bill Spernow, who beganone of our nation’s first outreach efforts in training municipal and state police in this important area. The contributions that both Fred Cotton and Bill Spernow have made in this field are measured by the esteem in which their professional colleagues held them. The contribution of SEARCH Group is also evident in that during the entire decade of 1980 to 1990 they provided the only Peace Officer Standards and Training (POST) instruction to law enforcement officers in the state of California. Indeed, another major deficit of our nation’s ability to address computer crime centered on the fact that virtually every one of our states’ training agencies provided no training at all to their law enforcement agencies in computer crime. In fact, until the early 1990s, state POST agencies were not offering even occasional training courses or instruction in this area.
In the mid-1990s our nation experienced a greater collaboration between federal, state, and local law enforcement agencies in addressing mutual training strategies. The Information Technology Working Group was an important step forward, as then–U.S. Attorney General Janet Reno appointed a small group of approximately 40 people from agencies within the federal, state, and local communities to join together in developing a cooperative blueprint for how our nation might best confront the growing problem of individuals using computers as an instrument for committing crime. After a series of meetings, they decided on a strategy of “Training the Trainers” so thata new and larger population of officers could reach out to their colleagues and provide instruction in this new area of criminal activity. Accordingly, a training curriculum had to be developed, and the U.S. Department of Justice funded several meetings ofthe nation’s leading experts in an effort to develop a series of courses that would be provided for state, federal, and local law enforcement personnel. After two years of course development, the National White Collar Crime Center was allocated the responsibility for delivering these courses to law enforcement personnel at the local and state levels. The federal effort of training new agents and in-service agents was allocated to the FBI, U.S. Secret Service, IRS-CID, U.S. Customs Agency, U.S. Postal Inspectors Division, and Federal Law Enforcement Training Center. Having had the privilege of serving as a member of the Information Technology Working Group, as well as having been active in our highereducation community, I saw a critical need to begin to mobilize our university community to address the unique needs of our law enforcement and prosecutorial agencies in addressing this growing problem of computer crime. Ironically, our nation’s universities had numerous computer science departments and over 1,000criminal justice programs, but there existed no coherent educational strategy to provide the theoretical and pragmatic skill sets that were required if our justice community was to seriously make inroads into this growing problem. Computer science departments were focused on educating their students in programming languages, database skills, and a number of other areas that provided assistance only to a small subset of our justice communities need. At the same time, most, if not all but a few, educationalinstitutions with criminal justice departments simply were not equipped with the faculty to address the problem of computer crime.
As a result of working in the area of computer crime since 1980, coupled with the knowledge of universities’ computer scienceand criminal justice departments, in 1996 the University of New Haven formulated both a graduate and undergraduate certificate in forensic computer investigation. This certificate program includes a sequence of courses that address three target disciplineareas: computer science, law, and forensic investigation. These course offerings were initiated in 1997 at both the main campus in Connecticut and the branch campus in Sacramento, California. Since we have had the privilege of working with our nation’s leaders in this field, we have utilized over 21 outstanding experts who have joined us in the capacity of practitionersin-residence; or distinguished special lecturers to offer this program. In 1998 we responded to the need for providing online educational courses and began offering both a graduate and undergraduate certificate in Information Protection and Security at both campus locations. In 2001 we began offering a Master’s of Science in criminal justice with a concentration in forensic computer investigation at our main campus. Finally, in 2002, we began offering the nation’s first Master’s of Science degree in National Security with a concentration in Information Protection and Security. This graduate degree is offered both at the main Connecticut campusand the California campus at Sandia National Laboratory in Livermore, California. These programs developed at the University of New Haven serve as a model in our attempt for universities to play a larger role in providing both the training and educationalcourses to the men and women of our justice community.
Several of our nation’s universities, aside from the efforts of the University of New Haven have made notable contributions in this area. Among these are Carnegie-Mellon Institute, with its formidableefforts in computer emergency response teams (CERT); Purdue University, led by the pioneering efforts of Eugene Spafford; the University of California at Davis, led by Matt Bishop’s work in computer security; the Naval Postgraduate School Campus at Monterey, with its outstanding computer science department; and Dartmouth University’s new program in research led by Michael Vattis. These are only a small section of the outstanding contributions being made by our academic community today.
II.Crime Scenes with Digital and Electronic Evidence
The electronic crime scene that possesses digital and electronic evidence creates new challenges for the investigator. There exists uniqueness to this new environment not only because the evidence may be difficult to detect but also because of how its evidentiary value may be hidden through steganography and/or encryption. Furthermore, there is a degree of anonymity in which perpetrators can hide their true identity in the forging of certain criminal acts and endeavors. Therefore, the rapid technological advancements occurring in our society through the digitalization of data and information are presenting new challenges to investigators. This electronic evidence is both difficult to detect and quite fragile; therefore, the latent nature of electronic evidence requires very skilled investigators.
Additional challenges that continue to confront the investigator encountering an electronic crime scene center on the global nature of the evidence. In many criminal cases involving computers and electronic technology, we encounter multijurisdictional issues that challenge the very legal structure of all nations’ legal and statutory codes. For example, today we find criminal enterprises being initiated from different nations throughout the world, and to effectively investigate, apprehend, prosecute, and convict these individuals we must utilize appropriate judicial search warrants. It is also necessary that the penal codes of the respective nations have statutory authority for legalaction to be pursued.
The “I love you” virus in 2000, which caused an estimated $10 billion in damages, was released by an individual in the Philippines and created havoc to computer systems throughout the world. Despite the extensive damage, this case wasnot prosecutable because the Philippines did not have legal restrictions against behavior of this type when this virus was released.
Also, the attack on Citibank in New York by Vladimir Levin and members of a mafia group in St. Petersburg, Russia, createdan enormous legal problem for the FBI because their investigator had to examine banking systems in over seven different nations where the electronic transfer of money was deposited. The application for search warrants and the timely tracking of this eventwas a challenge to even the most skilled set of investigators. Levin was arrested and sentenced to 3 years in prison and ordered to repay Citibank $240,000.
An additional problem with this new-age criminal activity that relies on technology and electronics is the ease with which one person can impersonate another through rather elaborate spoofing schemes. A related activity that has cost our nation’s businesses an enormous financial loss is identity theft. This crime of identity theft generally takes the victim approximately 6 to 9 months of work with credit agencies, bill collectors, and other credit entities before they can have any semblance of restoring their good name and credit standing.
Since personal computers can store the equivalent of several million pages of information, and networks can store many times more than this amount of data, the location and recovery of evidence by a trained computer forensic specialist working in a forensic laboratory may take several days or weeks. As mentioned earlier, searching computer files is an extraordinarily difficult process, because files can be moved from one computer to another throughout the world in a matter of milliseconds. Files can also be hidden in slack space of the computer hard drive or stored on aremote server located in other geographic jurisdictions. Files can also be encrypted, misleadingly titled, or commingled with thousands of unrelated, innocuous, or statutorily protected files. It is to address these challenges that the FBI has developed aComputer Analysis Response Team (CART Team); the IRS has a Seized Computer Evidence Recovery Team (SCER Team); and the Secret Service has an Electronic Crime Special Agent Program (ECSAP) (U.S. Department of Justice 2002, 35).
It is evident that these new technologies are requiring more skills for our investigators, prosecutors, and judges. Accordingly, the role of our educational institutions in preparing current and next-generation criminal justice personnel to address these challenges is becoming more critical as each new technology is developed and introduced to our society.
III.Computers, Electronic Equipment, Devices, and Information Repositories
In July 2001 the U.S. Department of Justice, through the Office of JusticePrograms in the National Institute of Justice, released the Technical Working Group for Electronic Crime Scene Investigation’s (TWGECSI) report,Electronic Crime Scene Investigation: A Guide for First Responders. The gathering of our nation’s experts to organize their advice to assist law enforcement personnel and agencies in preparing to address this new paradigm change in crime was one of our nation’s first important efforts to address this problem. The identification of the types of electronic equipmentand its purpose was to inform law enforcement personnel of the potential use and value of such equipment.
Both first responders to crime scenes and investigative personnel must appreciate the unique attributes of electronic equipment and be prepared to identify and assess its importance at a crime scene. This suggests the types and purposes of electronic equipment should be well understood as to their functionality and value to their owner. Also, from the viewpoint of assessing the potential impact on the victim, a thorough knowledge of this new environment will prove most useful and beneficial to law enforcement because the crime scene must be protected and processed consistent with forensic science principles. Because electronic evidence is so fragile, wemust train officers in the preservation and collection of electronic evidentiary materials. Digital evidence can easily go unrecognized, or be lost, if not properly processed. We must also ensure the integrity of digital evidence, because it is easily alterable. Therefore, the importance of training first responding officers to what is now becoming an electronic crime scene is an extremely critical function, and one that must be addressed by state and local law enforcement agencies throughout our nation.
Today, given the ubiquitous presence of computers, answering machines, hand-held personal digital assistants, facsimile machines, and other electronic equipment, almost any crime scene may conceal information of value in a digital format. The acquisition ofthis information is totally dependent on the actions of the first responding officer, who must have the ability to visualize and perceive the presence of such evidentiary material.
A.The Value of Equipment and Information
The type of computer system or electronic environment the investigator may encounter at a crime scene has a certain tangible and intangible value to the owner, victim, suspect, or witness. Because this value is measured not only in financial terms but also in terms of informational value,there are numerous perspectives that the investigator must be prepared to analyze. It is possible that the owner of a computer system may become a victim or a suspect in a case involving criminal activity. For example, the computer system can be the target of criminal activity, or it can be an instrument to use to commit criminal activity. Data residing on the hard drive will provide the answer and appropriate documentation as to each possibility. More often than not, the information that resides within these computer and electronic systems is of greater value than the systems themselves. The proliferation of new technologies at extremely economical prices will continue to make the investigator’s job more difficult. We now are in an era where computer communications can occur by using RAM CACHE, thus avoiding writing to the hard drive, and this can occur in a networked environment from any point to any other point within our world. Also, the development of encrypted hard drives will make the investigator’s job both more difficult and more expensive. As RAM CACHE communications become used by those seeking to commit criminal activity, the impact will be felt by law enforcement, homeland security, national security, and intelligence agencies.
B.Information Repositories — Informational Value
Just as information residing within electronic systems has value to the owner, victim, or suspect; there also exists value to law enforcement, prosecution, defense, and the judiciary as they engage their respective roles inthe full investigative and judicial process.
The valuable information residing within these computers and electronic systems will permit our judicial system to measure the accuracy of allegations, establish the circumstances and truth as to the purported criminal activity, and demonstrate with documented digital evidence the nature of the criminal activity or violation. This, of course, is totally dependent on the correct processing of the electronic crime scene, both technically and legally. The search andseizure of any electronic systems must withstand the scrutiny of the Fourth Amendment and all appropriate case and statutory law.
It is incumbent on our law enforcement agencies to provide the technical competence to evaluate this new form of criminal activity; while at the same time being fully compliant with all appropriate legal mandates.
C.Information Collection
The investigator may enhance the collection of information on a suspect or criminal by searching for electronic data that may reside in four specific locations:
Computer hard drive
File servers (computer)
Databases from governmental agencies, as well as private and corporate databases
Electronic record systems from governmental to private and commercial sectors
The first responding officers to a crime scene in which electronic equipment is present must recognize the presence and potential value of this electronic equipment. They also must provide the necessary security to ensure protection of potential evidence located on hard drives and file servers as the case moves from a preliminary investigation to a full investigation.
The searching and seizure of computer hard drives for the collection of information must be done within the parameters of a lawful search either incident to arrest or with appropriate judicial search warrants, or both. The investigator performing the search of a computer hard drive must be sufficiently trained and educated in the use of appropriate software utilities used in scanning hard drives. Furthermore, the officer must use the department’s approved protocol for conducting such a search. This includes creating a disk image on which to perform the search of the targeted hard drive while maintaining the integrity of the original hard drive and ensuring that none of the data residing on the hard drive is modified by the software utilized to search for appropriate information. The imagedhard drive should also be duplicated for eventual defense motions of discovery, in the event the defense counsel wishes their forensic computer experts to review or perform independent analysis of the hard drive.
The collection of information on individuals, whether they are suspects, victims, or individuals of particular interest, can be obtained through a wide array of governmental and private electronic record systems. Financial reports and credit histories contain a vast storehouse of data not only on the individual in question but also on spouses, relatives, and friends. Because law enforcement agencies also have the responsibility of protecting the privacy of individuals, great care must be exercised in searching the enormous range of databases that now exist within our society. This implies that legal rules must be vigorously adhered to through use of subpoenas and application for judicial review or search warrants.
D.Management of the Electronic Crime Scene
Managing an electronic crime scene is quitesimilar to any other crime scene, with the exception that specific skill levels and training background will be required of the forensic computer investigator. In addition, the type of crime committed will invariably call for an exceptional team effort bythe seasoned crime investigator in cooperating with the electronic crime scene investigator. Because most police organizations do not have adequate resources to fully staff their departments with individuals who possess such demanding skill attributes, itis not uncommon to find that regional task forces have been developed to address these issues. However, this can lead to complications regarding jurisdictional issues, command and control, collection of evidence, and sharing of information with other members of the crime scene team. Because most electronic crime scenes are photo-rich environments, all of the traditional crime scene mapping, photographing, and diagramming are essential to the proper investigation. The crime scene may contain computers thatmay need to be searched not only for information residing on their hard drive but also for fingerprints and DNA from the keyboard, diskettes, and other areas of the computer. Therefore, a protocol for addressing such issues must be preplanned and availableto all personnel, should implementation of such requirements be necessary.
E.Electronic Crime Scene Procedures
The value of the National Institute of Justice’s_Electronic Crime Scene Investigation: A Guide for First Responders_centers on the awareness and assistance that the typical first responding officers will need in both identifying and protecting electronic instruments found at the crime scene. Their publication provides brief descriptions, photographs, primary use, and potential evidence for:
Computer systems and their components
Access control devices, such as smart cards, dongles, and biometric scanners
Answering machines
Digital cameras
Hand-held devices, such as personal digital assistants (PDAs) and electronic organizers
Hard drives, both external and removable hard drive trays
Memory cards
Modems
Network components with local area network (LAN) cards, network interface cards (NICs), routers, hubs, and switches
Servers
Network cables and connectors
Pagers
Printers
Removable storage devices and media
Scanners
Telephones, such as cordless and cell phones
Miscellaneous electronic items, such as the following:
Copiers
Credit card skimmers
Digital watches
Facsimile machines
Global positioning systems (GPS)
This booklet for the first responding officer provides a rich orientation to the types of devices one might encounter at an electronic crime scene. It also highlights the idea that data can reside in unusual electronic places that may have informational value to the crime sceneinvestigator. At the same time, the first responder should note that data can be lost by unplugging the power source to an electronic instrument, and great care must be taken to protect the crime scene (National Institute of Justice 2001, 9–22).
There areoccasions when the first responding official to a call-for-services event may not be a police officer; that official may in fact represent either a medical emergency or fire assistance call. In the event that these respondents perceive the incident as a potential crime scene, they will have the responsibility to call for police services, in which case there may be a multiagency responsibility for securing the potential or real crime scene. A recent example of this situation occurred in the “Frankel Case” in Stamford, Connecticut, where the first responding personnel to a fire alarm notification were fire personnel. After observing computers throughout the estate, including even in bathroom areas, plus what appeared to be a deliberate effort to burn computercomponents within the kitchen area of the estate, the fire personnel notified the fire arson investigator, who not only notified the local police department but also encouraged the local department to notify the federal authorities. Fortunately, this arson investigator had received educational courses in the area of computer crime and quickly realized the nature of the electronic evidence and took appropriate action.
It is interesting to note in this case that although the local police department had personnel trained in many areas, they did not have any personnel trained in electronic crime scenes. The arson investigator prevailed on them to contact a federal agency,who initially declined involvement in the case. The arson investigator was familiar with a guest instructor who had lectured in a computer crime course, so he called on her and described the situation. This guest instructor, who was also a federal agent well-trained in the area of computer crime, realized the importance and significance of the situation and subsequently notified the original federal agency as to the seriousness of this case. The federal agency reevaluated the situation and joined in a multiagency investigation that resulted in the arrest of the subject by German police authorities. Thus, the perseverance of the first responding personnel, along with their training and education, resulted in an international investigation of a multimillion-dollar fraud and embezzlement case. The scope of the computer involvement in this case can be assessed by the fact that it required 16 federal agents over 3 months to process all of the computer evidence in this case.
In most cases, the first responding officer’s initial duty is to provide aid or assistance to a victim or victims if present. Second, it is incumbent on the responding officer to take into custody any suspect at the crime scene and to identify witnesses or ask them to remain until crime scene investigators arrive at the scene. Finally, the first responding officer must secure the crime scene to prevent contamination of the scene or destruction of materials that may possess evidentiary value. As the preceding case revealed, many times it is the education, experience, and initiative of a first responder that can go beyond the traditional role expectations and requirements and play an important role in the successful resolution of a case. This suggests that we really need more than technicians who will respond to crime scenes; we need those who have the benefit of a rich education and broad training perspective.
It is generally accepted as good police practice that, when entering an electronic crime scene in which there are no injured parties or suspects in need of detention, the following guidelines be followed:
Secure the scene so as to minimize any contamination of the scene.
Protect the evidence, and, if people are at the scene, do not permit anyone to touch any computers or other electronic instruments. Have all electronic devices capable of infrared connectivity isolated, so as to control for data exchange. This will include cell phones, PDAs, and other similar instruments.
Evaluate the electronic and computer equipment at the scene and make a determination as to whether assistance will be required in the processing of the scene. Few officers can be expected to handle the more complex and sophisticated electronic environments. In some cases, the need for a consultant may be required. Also, personnel with appropriate skills may be located from a regional or federal task force.
Observe whether any computers are turned on, and, if so, take the following precautions so as not to inadvertently lose any data on the computers:
Photograph the computer screen if it is left on and it appears useful.
Document the scene through videotape, photography, and crimescene sketches.
Label and photograph all cards and wires running to and from the computer to peripheral devices.
Do not turn off computers in the conventional manner becausethe computer could be configured to overwrite data. Therefore, in stand-alone computers, it is best to remove the power plug from the wall. Also, if a telephone modem line is in use, disconnect the cable at the wall. It is important whenauthorities encounter a network as opposed to a stand-alone computer that no one removes the power cord from the server. If the agency does not have personnel who are trained to work within a network environment, other assistance should be requested, andthe scene should remain secured until such assistance is available.
Collect any material germane to the electronic or computer environment, including manuals, peripherals, diskettes, and any medium capable of storing data.
Inform the crime scene supervisor, in the event the crime scene will require the use of fingerprinting powders to develop potential latent prints on the computers, that no aluminum-based powders should be used to dust for fingerprints on the computer, because it could create electrical interference. In fact, the forensic processing of the computer and its hard drive should occur prior to any dusting for fingerprints. However, the forensic computer investigator and/or the person who will actually process the computer should also take care as to not preclude a subsequent search for traces of DNA evidence and an examination for latent fingerprints.
Take care in disassembling and packaging items for transport to either the police evidence and property room or the crime laboratory for the processing of the equipment:
Maintain the chain of custody on all evidence; therefore, followand document the appropriate protocols.
Package, transport, and store electronic instruments and computerswith minimal to no exposure to situations that might compromisethe data residing within their storage mechanisms. Electronic instruments and computers are very sensitive to environmental temperatures and conditions and other radio-wave frequencies.
Place a seizure diskette in and evidence tape over drive bays of computers that will be seized prior to removal and transportation.
Transport computers and other electronic instruments and evidence with caution so as not to damage or lose the fragile electronic data. It is advisable not to transport this equipment in the trunk of a police car because this is the area where the police unit’s two-way radio is located, and the signals may damage the data reposing in the computer and other electronic instruments.
Store and maintain computers and electronic equipment in an environment that is conducive to preserving the data contained in that equipment and is free from any nearby magnetic fields.
In those cases where the forensic computer investigator may participate as a member of a raiding team, there will obviously be time to prepare and plan for appropriate action, as opposed to being called to a crime scene as a result of the first respondingofficer’s request for assistance. In the case of a preplanned raid, the forensic computer investigator will clearly be aware of the criminal activity and will have the opportunity to engage in presearch intelligence. This will permit the opportunity to engage skilled personnel who will be able to process the scene on arrival. The presence of a network may be determined, and appropriate plans can be developed for processing this environment. Also, it may be possible to gather useful information about the situation from the Internet Service Provider (ISP). In short, knowledge about the location, equipment, type of criminal activity, and other pertinent facts will enable the forensic computer investigator to assist the prosecuting attorneys in the preparation of search and seizure warrants. Also, the involvement as a member of the raiding team will permit a more tailored plan in which minimal loss of data to the computer and electronic environment will occur.
F.Initiating the Forensic Computer Investigation
Once a forensic computer investigator is called on to initiate a formal assessment of a case involving a computer, either as an instrument of crime, a repository of data, information associated with a crime, or a target of a criminal act, it will be necessaryfor the forensic computer investigator to prepare an investigative protocol to correctly gather and preserve any appropriate evidentiary material.
In the collection of evidence from a computer hard drive it is important to make a bit-stream copy of the original storage medium and an exact duplicate copy of the original disk. After the evidence has been retrieved and copied, the bit-stream data copy of the original disk should be copied to a working copy of the disk so that the analysis of the data will notcontaminate the evidence. In the analysis of the digital evidence, you may have to recover data, especially if the users have deleted files or overwritten them. Depending on the type of operating system being used by the suspect, the computer investigatorwill determine the nature of the forensic computer tools that will be applied. For example, in examining Windows, DOS systems, Macintosh, UNIX, or LINUX systems, one has to understand the file systems that determine how data is stored on the disk. When itis necessary to access a suspect’s computer and inspect data, one will have to have an appreciation and working knowledge of the aspects of each operating system (Nelson, Phillips, Enfinger, and Steuart 2004, 50–51, 54). For example, in Windows and DOS Systems one must understand the following:
Boot sequences and how to access and modify a PC’s system (CMOS and BIOS)
How to examine registry data for trace evidence in the user account information
Disk drives and how data is organized, as well as the disk data structure of head, track, cylinder, and sectors
Microsoft file structure, particularly clusters, file allocation tables (FATs) and the NTFS; because data can be hidden, as well as files, that may suggest a crime has occurred
Disk partition in which hidden partitions can be created to hide data
An excellent and detailed explanation of the UNIX and LINUX operating systems can also be found in theGuide to Computer Forensics and Investigations(Nelson, Phillips, Enfinger, and Steuart 2004, 74–76, 80).
Additional information on initiating a forensic computer investigation will be provided in greater detail in subsequent chapters of this text. In the interim, a brief taxonomy of crimes impacting the forensic computer investigator may be useful to review.
The computer as an instrument in criminal activity
Child pornography and solicitation
Stalking and harassment
Fraud
Software piracy
Gambling
Drugs
Unauthorized access into other computer systems
Denial-of-service attacks
Data modification
Embezzlement
Identity theft
Credit card theft
Theft of trade secrets and intellectual property
Extortion
Terrorism
The computer as a target of criminal activity
Theft
Virus attack
Malicious code
Unauthorized access
Data modification
Intellectual property and trade secrets
Espionage to government computer systems
The computer as a repository of criminal evidence
Child pornography and child exploitation materials
Stalking
Unauthorized access into other computer systems
Fraud
Software piracy
Gambling
Drugs
Terrorism-attack plans
Terrorist organizations’ Web-site recruiting plans
Credit card numbers in fraud cases
Trade secrets
Governmental classified documents as a result of espionage activities
A most informative and detailed taxonomy that examines 14 criminal activities and directs the forensic computer investigator to assess these criminal activities against 5 categories where general information may be located and 70 categories in which specific information can be considered is provided in the National Institute of Justice’s guide,Electronic Crime Scene Investigation: A Guide for First Responders(National Institute of Justice 2001, 37–45).
G.Investigative Tools and Electronic Crime
Scene Investigation
Forensic computer investigators have a number of software tools and utilities available for their use in analyzing a suspect’s computer. A list of some of the tools available is as follows:
Safeback
Maresware
DIBs Mycroft, version 3
Snap Back Dot Arrest
Encase
Ontrack
Capture It
DIBS Analyzer
Data Lifter
Smart
Forensic X
Each agency will equip their forensic computer investigators with hardware tools appropriate to disassemble a computer system and remove necessary components. In many cases the tool kit will also include necessary materials for packaging,transporting, storing, and evidencing materials. Depending on the workload and caseload of each agency, the use of software and tool kits will vary depending on the agency’s needs and policies.
IV.Legal Issues in the Searching and Seizure of Computers
The Fourth Amendment to the United States Constitution limits the ability of law enforcement officers to search for evidence without a warrant. The Fourth Amendment specifically states:
The right of the people to be secure in their persons, houses, papers,and effects against unreasonable searches and seizures, shall not be violated, and no warrants shall issue, but upon probable cause, supported by oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.
A.Searching and Seizing Computers without a Warrant
The United States Supreme Court has held that a search does not violate the Fourth Amendment if it does not violate a person’s reasonable expectation of privacy. The U.S. Department of Justice’s Computer Crime and Intellectual Property Section suggests in their July 2002 revised manual that a reasonable expectation of privacy of information stored in a computer is determined by viewing the computer as a closed container such as a file cabinet. The Fourth Amendment generally prohibits law enforcement from accessing and viewing information stored in a computer without a search warrant. However, this reasonable expectation of privacy can be lost if a person relinquishes control to a third party by givinga floppy diskette or CD to a friend, or bringing the computer to a repair shop (U.S. Department of Justice 2002, 8–10).
The Fourth Amendment applies only to law enforcement officers and does not apply to private individuals as long as they are not actingas an agent of the government or with the participation or knowledge of any government official. Therefore, if a private individual acting on his or her own conducts a search of the computer and makes the results available to law enforcement, there is no violation. InUnited States v. Hall, 142 F. 3rd, 988, (7th Cir. 1998), the defendant took his computer to a computer repairman who, in the process of evaluating the computer, noticed computer files that on examination contained child pornography. The repairman notified the police, who obtained a warrant for the defendant’s arrest. The court upheld the action and rejected the defendant’s claim that the repairman’s search violated his Fourth Amendment rights (U.S. Department of Justice 2002, 13).
There are exceptions to requiring a warrant in computer cases, and these situations involve consent, exigent circumstances, and the plain-view doctrine, incident to arrest. The issues that emerge in consent center around parents, roommates, and siblings, and whether they have the authority to consent to a search of another person’s computer files. The courts have held that parents can consent to searches of their minor child’s room, property, and living space. However, if the child is living with the parents and is a legal adult, pays rent, and has taken affirmative steps to deny access to his parents, the courts have held that parents may not give consent to a search without a warrant (United States v. Whitfield, 939 F. 2nd, 1071, 1075 [D.C. Cir. 1991]).
The exception to requiring a search warrant in exigent circumstances is permissible if it would cause a reasonable person to believe that entry was necessary to prevent physical harm to the officers or other persons or to prevent the destruction of evidence.
The exception for requiring a warrant under the plain-view doctrine permits evidence to be seized if, in the process of conducting a valid search of a computer hard drive, the officer finds evidence of an unrelated crime while conducting the search (Horton v. Californ__ia, 496 U.S. 128 [1990]). However, the exception to a warrant under the plain-view doctrine does not authorize agents to open and view the contents of a computer file that they were not otherwise authorized to open and view. InUnited States v. Carey, 172,F. 3rd 1278, (10th Cir. 1999), a detective, while searching a computer hard drive for drug trafficking evidence, found a JPG file and discovered child pornography. The detective then spent 5 hours and downloaded several hundred JPG files in a search not for drug trafficking, which the original search warrant authorized, but for more child pornography. The defendant argued to exclude the child pornography files on the grounds that they were seized beyond the scope of the warrant. The government argued the detective seized the JPG files because they were in plain view. The Tenth Circuit rejected the government’s argument, stating that the first JPG file was appropriate, but they could not rely on the plain-view doctrine to justify the search for additional JPG files containing child pornography evidence beyond the scope of the warrant (U.S. Department of Justice 2002, 21–22).
In the situations of searches incident to an arrest, the courts have permitted a search without a warrant as an exception for electronic pagers. However, the courts have not resolved this issue with reference to electronic storage devices, such as PDAs, cellular phones, laptop computers, or those devices that contain more electronic information than pagers.
B.Searching and Seizing Computers with a Warrant
To obtain a search warrant from a judicial officer requires the preparation of two important documents. The law enforcement officer must prepare first an affidavit, which is a statement made under oath that describes the basis on which the officer believes the search is justified by probable cause. The second document is the actual search warrant, which must describe the place to be searched and the items or persons to be seized. In federal search warrants it is also recommended that the officer or agent include an explanation of the search plan or strategy.
In criminal investigations involving the use of computers, it is important to describe in the search warrant whether the property to be seized is the computer hardware or the information that the computer contains. If the computer is an instrument of a crime, then the search warrant would specify the computer hardware itself. On the other hand, if the officer’s probable cause is based on the information stored in the computer, then the search warrant would focus on the content of the relevant files rather than the storage device (United States v. Gawrysia__k, 972 F. Supp. 853, 860 [D. N.J. 1997], Aff’d 178 F. 3d 1281 [3D Cir. 1999; alsoDavis v. Gracey, 111 F. 3D 1472, 1480 [10th Cir. 1997]; U.S. Department of Justice 2002, 50–51).
Although criminal investigations and the requirements for fulfilling search warrant requirements will vary from state to state, as well as from state to federal jurisdiction, under the federal rules of criminal procedure, Rule 41 would be the guiding force in the previously described search warrant preparation and application. Another important consideration in preparation of search warrants will be whether the target of the investigation is a business, because the economic aspect of seizing computers could have devastating consequences for a legitimate business.
In fact, search warrant requirements for business establishments have to address the issue of reasonable expectation of privacy that people have in their office space. The issue of consent by business managers, supervisors, co-workers, and whoever has common authority over an area can be an important aspect if the search were conducted without a warrant. Another aspect of searching workplace environments would be the public workplace as opposed to the private workplace. The reasonable expectation of privacy would be at variance in the public workplace as opposed to the private workplace.
The complexity of forensic computer investigations entails an appreciation and understanding of the legal requirements both in terms of the elements of an offense and the procedural requirements for effecting a search and seizure of evidentiary material. In addition, the forensic computer investigator is also required to understand the intricacies of the computer itself, and how it might be used either as an instrument to commit a criminal offense or as a repository of criminal information.
V.Summary
This chapter has provided an introduction into the paradigm change that is occurring with reference to crime: Today’s criminalsare using computers as their instruments to take advantage of new technological possibilities. The forensic computer investigator has to be prepared to investigate these criminal acts in which the computer may be a target of the criminal. This implies that individual, corporate, and government computers are at risk as targets of opportunity. The data that resides in these computers has value and is subject to loss, in some cases at enormous expense. Therefore, the forensic computer investigator must be cognizant of this environment and how to develop systematic plans for investigating those who use computers and sophisticated electronic equipment in the commission of criminal acts. The computer also serves as a repository of data in which the criminal has either stored the fruits of his or her criminal activity, or providesevidence as to the unlawful actions the criminal has utilized in using his or her computer to attack or harm another individual, corporation, or government.
The categorization of an electronic crime scene rich in new technologies that store data and information of potential evidentiary value suggests that we must educate our law enforcement officers to recognize characteristics of and function effectively in this new environment.
References
National Institute of Justice. July 2001.Electronic Crime Scene Investigation: A Guide for First Responders. Washington, D.C.: U.S. Department of Justice.
Nelson, Bill, Amelia Phillips, Frank Enfinger, and Chris Steuart. 2004.Guide to Computer Forensics and Investigations. Canada: Thomson Course Technology, 25 Thompson Place, Boston, MA02210.
Parker, Donn B. 1997. Fighting Computer Crime: A New Framework for Protecting Information. New York: John Wiley and Sons.
U.S. Department of Justice, Computer Crime and IntellectualProperty Section, Criminal Division. July 2002. CCIPS Manual.
| The Digital | 2 |
|---|---|

CHRIS MALINOWSKI
At first glance, the staffing of any unit appears to be quite elementary: Enumerate the tasks to be performed, and then find the appropriate personnel with the skills required to perform the tasks. Unfortunately, this process is not as simple as it seems.
The problem in staffing and training an investigative unit, whether it is called a computer crime unit, computer investigations squad, computer lab, computer forensics unit, or some other title, is not a trivial one. Even the choice of a name is importantbecause it indicates purpose and functionality.
The traditional method of establishing any unit is made more complicated by the nature of the work to be performed. The rapidly changing technical environment, staffing pressures, and support (or lack thereof) of the administration make establishment and maintenance of a unit challenging, to say the least.
As part of this chapter, I present some of my experiences that might help the reader understand the need for certain skills that should be either recruitedor developed; herein lies a great part of the challenge faced by the unit.
Typically, a police department recognizes the need to stay current with the latest trends in crime. It will mandate that the department establish a computer crimes unit. Organizational charts are amended, policies rewritten, and budget lines promulgated. However, once the department establishes the unit, it may fail to realize that the unit requires extensive and continual support in order to fulfill the intended mission.
21
Ratherthan simply discuss the theoretical and possible routes to the destination, I will mention some of the speed bumps and detours along the road to the destination that I, as well as others, encountered in the journey. The unit as described provides a backdrop against which to measure and compare other units.
I.Unit Name
The NYPD’s (New York Police Department’s) Cybercrime squad was founded as the Computer Investigations and Technology Unit (CITU). Essentially, it was tasked to perform computer investigations and handle technology issues for the Detective Bureau. These basically devolved to any computer-based requests or problems generated within the Detective Bureau.
The calls received, even a year or two after the inception of the unit, often had little to do with the actual mission, or else in some minor instances duplicated tasks performed by the Department’s MIS Division. At one point the unit became a clearing house for the dispersal of personal computers to the various Detective Bureau commands. In an instance of laptops and the “no good deed goes unpunished” philosophy, since the laptops were purchased using federal funding, they were subject to inspection upon demand. The laptops were distributed to various Detective Bureau commands and assigned to individuals, and when those individuals were transferred or promotedand left the CITU, the devices somehow went with them. When selecting a unit name, select a name that clearly advertises the mission and avoid performing functions that other units are already performing on an agencywide basis.
II.Mission Statement
Defining the mission statement helps clarify the areas of responsibility and defines the role of the unit within the overall organization. The process of defining the mission will also help point out potential conflict areas within intraorganizational jurisdictional mandates. Organizational policy must be determined from the onset in order to avoid duplication of effort, parallel investigations that step on each other, wasteful expenditure of resources, and potential internecine battles. The mission statement should include the purpose of the unit as well as clearly outline those tasks to be performed by the unit. The agency then needs to ensure that everyone is made aware of the unit, its role in the overall agency, its functions, and the services it performs.
Failure to ensure this organizational awareness can result in mishandled investigations and squandered resources. If part of the mission is to provide field support, then make provisions to provide that support consistently by allocating the appropriate resources. If the mission includes supporting seizures pursuant to search warrants that are routinely conducted, you need to consistently ensure the means of providing that assistance in the proper time frame and in the response scale required. For example,responding to an expected seizure of computer equipment at various sites on Super-Bowl Sunday will stretch the resources of any unit; however, be prepared and make arrangements to properly staff that event. A provision can be built into the guidelines asking that any units requesting technical assistance provide a prior notification, perhaps of 2 business days.
The mission of the unit should be based on realistic expectations. By examining other cyber units and their experiences, you can provide guidelinesas to whether or not your unit will meet these expectations.
A critical component in formulating the unit is the administration’s support in providing the necessary resources in the creation, as well as continued operation, of the unit. Typically, the resources start and end with the_initial_financial considerations; monies are allocated for the initial outlay for equipment and training, as well as for continued purchases of equipment and supplies over time. Due to the nature of the industry and technologies involved, it is often difficult to foresee some needs in order to adequately fit them into an overall budget.
Administrators should understand that the needs of the unit will often conflict with established guidelines regarding allocation of resources. Units can fail when administrators attempt to fit the nature of the work to existing guidelines. Instead, thought should be given to altering or expanding the guidelines to match the new types of work to be performed. This can be defined as the difference between merely reacting and responding to changing conditions and technologies.
Problematic areas may be those dealing with resources: manpower allocation, overtime, purchasing of equipment, and outsourcing of services. I suspect that, as departments grow larger, they become more inflexible in dealing with issues, particularly in these areas. It is possible that a bureaucratic lethargy and inertia builds such that it is simpler to deal with problems by adhering to policy, despite the fact that operations maybe severely impacted. Eventually a special overriding exception may appear in the policy, rather than the original guideline being altered.
I have provided some typical examples in the list that follows. In determining the scope of your unit’s work, do you wish your unit to handle or be part of the incidents listed? If so, realize that oftentimes they may cross over into areas covered currently by other units.
- _An allegation of ongoing online narcotics sales is investigated and found to be substantiated. Is_the fieldwork to be pursued by the narcotics unit, or by the computer crime squad, which has substantiated the crime?
Negotiations and interactions often take place in the cyber world. Tracking the origin and presentation of such evidence may require special understanding and skills, both in order to determine the source as well as pass as Internet users.
- _An online auction house is used to offer items for sale. Computers and other tech equipment are being sold for relatively low prices, indicating possible_stolen merchandise.
Investigations of this nature involve tracking of e-mails, as well as potential online conversations. This requires ensuring admissibility of the evidence. During the course of the investigation, there will be an exchange of money for goods, at which pointit is hoped that the suspect will physically be present and be arrested.
These cases most often will be reactive in nature, because nobody wishes to devote resources to an investigation in which either the suspect or the victim (or both) do not fall within their jurisdiction.
The special victims/sex crimes unit is currently investigating a case in which a minor is alleged to have met with an adult. It is known that the two have had online chats and e-mail communications.
- Suspected, but unknown, if adult ha__d sexual contact with the minor.
Minor denies relationship.
- Minor claims relationship.
In either event, the minor’s computer should be examined. Obviously the regular detective squad is not equipped to perform such an examination. In the case in which theminor admits the incident, finding corroborative evidence on the computer may result in the sex crimes unit arresting the suspect.
In the event in which the minor denies the incident, and in which we fail to discover the smoking gun on the computer, we areleft with an option. In fact, this situation has occurred, and my unit eventually arrested and brought in the perpetrator when he met one of my detectives, whom he believed to be an underage boy. Subsequent investigation and interviews resulted in the discovery of other incidents and victims, including the original victim.
- Spam e-mail issued to 10,000 people worldwide offers a list of kiddie porn video titles for sale. Included is the address in order to send the money. The location is within your jurisdic__tion.
This is one specific example of_why_responsibilities must be clearly defined. The vice squad rolled on this allegation and obtained a_no knock_warrant, allowing them entry without notification. This they promptly did at 6 a.m. When I arrived at 8 a.m. and was made aware of this complaint, I discovered that this unit had already executed the search warrant. Needless to say, had they looked into the matter they would have discovered that their message did not originate from that location, or with the people at that location.
- Special victims receives a complaint of a “he said–she said” nature. Complainant alleges a date rape, obviously denied by the suspect. The two met online, and there are communications that took place online.
Because of the nature ofthe rape allegation, the special victims unit arrested the suspect. Pursuant to the arrest, I received a call to perform the computer-based side of the investigation. This involved seizing and searching the suspect’s computer (both at home, as well as at the business). The suspect, an established businessman, was arrested on a Friday and wound up spending the weekend in lockup.
In examining the hard drive we located what seemed to be exculpatory evidence indicating that the alleged victim was more than willing to engage in the behavior that was the basis of the arrest. The businessman was suing the City of New York for several million dollars, and after 7 years had recently reached a settlement prior to jury deliberation after a trial.
When I was called on to provide a sworn affidavit, one issue that was raised by the (now) plaintiff’s counsel was the level or training and experience of those performing the actual computer examination, as well as my personal expertise. This is one reasonwhy training of personnel is extremely important.
- Special victims is investigating a date rape at a university in which online communications existed.
Retrieving information from mail servers, as well as seizing and examining electronic evidence, requiresexpertise. This is a support function, and not the prime investigative function, both from an investigative viewpoint as well as from the fact that this is a special victims–type case that requires their special knowledge of such cases. For that reason, this case falls within_their_mandate and not within a local precinct’s detective squad mission.
Notwithstanding, case law regarding handling of e-mails and other electronic communications are not part of the standard training in the academies, which underscores the need for training of any specialized unit that routinely deals with and provides advice in these matters.
Likewise, the support falls within a cybercrime unit’s mission profile. Execution of a search warrant on the site of the university yielded acomputer used by the suspect, as well as recording devices, such as Jazz drives. The special victims squad seized the recording equipment. Unfortunately, although they are experts in matters of sexual crimes and crimes against minors, they are not computer technicians and neglected to seize the Jazz disks (media containing the data). This is comparable to taking the telephone answering machine, and leaving behind the tapes.
The reason I mention this is not to disparage the special victims unit — they do excellent work. Rather, I wish to reinforce the point that even if your unit has a mission statement and the department has a defined policy for dealing with digital evidence, there will generally be instances of this nature in which others fail to call forthe proper support.
The rationale for failing to secure another unit’s assistance may be as simple as a desire not to share the glory, or merely simple ignorance of policy. As stated elsewhere, the “glory” or “notice” issue is not to be underrated. Often the allocation of resources depends on being noticed by those controlling the resources.
- A bias incident needs to be investigated.
Investigations of this nature may be handled by a specialized unit. Whether or not the department decides to employ a bias unit to deal with minority or otherwise politically sensitive groups, it must make a decision regarding the scope of a cyber unit’s participation. The depth on involvement should be in the identification of any source of electronic information.
Certainly, a bias unit has the training to understand the departmental need to deal directly with the groups of people classified under bias incidents. Conversely, the cyber unit also has the training to understand the evidentiary needs particular to this type of digital evidence.
A caveat is in order here, as well in other cases; although it might be desirable to gather information on a particular group by monitoring their presence on the Web, this is an_intelligence_function. Decide whether or not your mission is to include this and, if so, whether the proper resources will be available.
One example is a request we received pursuant to a homicide at a nightclub to look up all things pertaining to the Goth culture on the Internet.
- The mayor or other public official has r__eceived a threat online.
Unless there is a specialized unit handling these issues, the immediacy of the threat dictates that the cyber unit should have at least a supporting role, if not the lead role, in the investigation.
- An investigation of public offic__ial or agency has begun.
Once again, there may be a specialized unit, or an inspector general’s office handling such matters. Unless the cyber unit belongs to the department being investigated, it may be appropriate to limit participation to a supporting role in the investigation.
- An online threat has been made to a school.
An immediate response is required in these cases. Successful investigation, as well as prosecution, relies on the cyber unit being involved early on in order to locate the source of the threat, if it was communicated electronically.
A case of intellectual__property theft is being investigated.
Duplication of software
Dissemination of copyrighted material via computer networks
Proprietary information stolen
The nature of these crimes involves locating the information that is stolen, along with uncovering the trail by which it was taken, in many cases. The stolen information may be confidential or may be a work product, such as software. The type of information may result in nontangible evidence, which may require the resources of the cyber unit.
As a brief aside, it may be prudent to consider a notification to the cyber unit regarding the loss of a laptop, because laptops often contain confidential information(both personal, as well as corporate).
- An alleged computer trespass is being investigated.
Proving that someone has been on a particular computer host without authorization requires skills positively not taught in the academies or given during detective training; therefore, it should remain in the domain of the cyber unit.
- The case involves computer tampering.
Just as the skills to pursue a trespass investigation are not part and parcel of the typical detective’s training, these crimes require network andforensic skills in order to develop the case.
In one instance we responded to a large corporation. The complaint centered on a trader who had altered a computer model to degrade the valuation of commodities being traded. This model was utilized in order toadvise clients so that they might make better-informed decisions.
The typical tampering case is what we would normally consider to be hacking. Although the word is not properly used, most people understand hacking to be an illicit entry and alteration ofa computer system and its data.
Identity fraud allegations are being investigated.
Steal identity for criminal benefit
Assume identity to impersonate another without monetary benefit (stalking and harassment)
Although many instances of identity theft are low-tech, those involving computers or digital evidence require support from a cyber unit. Evidence needs to be preserved, analyzed, and investigated.
- Online stalking is suspected.
Expertise in putting the perpetrator at the keyboard is critical. The case will either present existing evidence or require that an investigator assume the victim’s identity. Evidence requires expertise to place the suspect, whereas identity assumption to further the case will requiresomeone versed not only in tracking of persons on networks but also innetiquette, that is, the online culture and the technology involved.
Sting operations may be necessary.
Child exploitation
Child pornography
Child luring
Traveler cases
It is paramountin these cases to find the child, if missing, and to place the perpetrator at the keyboard. Handling of evidence requires special expertise, and in the event of assuming an online persona, the_creation_of the evidence requires special attention and processing.
Public moral offenses
Narcotics
Prostitution
Along with the business world, these enterprises have also gone online. The sole rationale for involvement is to determine the source of the network traffic, because intelligence and special concerns (suchas gangs or organized crime) may exist.
- Stolen property
Investigations involving the sale in which an online site is used in order to transact the sale may result in some level of involvement by a cybercrime unit; essentially, in those cases, investigators try to place the seller at the keyboard. The scope of involvement by the cybercrime unit may be limited unless this is a pattern or a proactive case.
- Sensational cases may require investigation of computer technology.
A sensational case brings computer-based equipment that belongs to the suspect or victim to your attention. Although it is rhetorical that a cybercrime unit does not catch the case, the unit may very well be asked to examine the evidence. The evidence needs to be examined for information that might be of interest to the investigating detectives.
In one incident, a homicide prompted the investigating unit to ask our unit to scour the Internet for any references to the suspect’s name. Using standard tools tosearch the Internet, I discovered approximately 6,000 hits on the suspect’s name. Most of these references were of no value to the investigation, yet they still required perusal. I estimated that looking through the entire range of returned data would require about 200 man-hours.
Although these examples are but a few, they help to illustrate the range of possible investigations. In some cases, the investigations are initiated by other units, and in others they may be self-initiated.
A broad and general mandate of a computer crimes unit might resemble the following:
Investigate cases in which computers are used either as instrumentality of a crime or are the target of a crime.
Assist in cases in which the computer may contain “fruits of the crime,” or electronic evidence.
Assist in cases in which part of the case resides in the electronic domain (i.e., used the Internet in order to communicate).
Seize and secure digital evidence.
Examine (search) digital evidence for the unit’s cases.
Examine digital evidencefor the entire department or for other agencies.
Provide expert testimony.
Depending on the scope of functions to be incorporated within the unit’s mandate, skill sets will vary. For example, if the unit responds to an incident within a corporate setting,it may very well result in a minimal-intrusion examination of volatile settings and information on a particular machine. The knowledge to do this and to guarantee the least intrusion as possible is not taught at academies, or even to officers who might befirst responders in such incidents. Additionally, the skill required to testify as to the manner in which any evidence was obtained is critical in order to communicate to a judge or jury any investigative results.
Investigators who assume identities onlinefor various purposes need to be familiar with the communications medium, as well as conversant with the nuances of that medium: knowledge of netiquette and acronyms and emoticons, or smileys, are not part of standard training. These investigations requirethat a sworn member act as the technician, because evidence gathered may escalate into probable cause that a crime has been (or is about to be) committed.
One unspoken mission mandate that functions across all levels of the bureaucracy and across organizations is to secure future resources. One sure method for doing this is to take on newsworthy investigations. The selection of self-initiated investigations may assist in this regard. Thanks to the relative newness of computer crime, many incidents afford the opportunity to showcase this aspect of law enforcement. In fact, many crimes committed are new variations on old themes; however, the technology is what makes them provocative and newsworthy. A caveat is that once brought to light,_all_aspects of the investigation are subject to closer scrutiny, both within the department and in the public eye. My point is that opportunities exist to develop public awareness (and subsequently departmental attention) of the unit.
A.One Unit’s History
The NYPD established the Computer Investigation and Technology Unit, or CITU, in 1995. The unit was set up within the Detective Bureau and, specifically, within the Central Investigation and Resource Division of the Bureau (CIRD). CIRD was housed in One Police Plaza (1 PP) and contained units such as Hostage Negotiations, Technical Assistance and Response Unit (TARU), Special Victims Liaison Unit, Crime Stoppers, and the Photographic Unit.
Initially, CITU was staffed with one lieutenant, two sergeants, and a handful of detectives and police officers. The commanding officer (lieutenant) had no computer experience to speak of and had been transferred from a detective squad in the field. The two sergeant supervisors hadpersonal computer(PC) experience. The detectives and police officers had a mix of PC experience as well as investigative experience. The investigative background varied because the personnel were pulled from both administrativestaff and field staff; one detective had served in the Transit Department’s police department in a variety of investigative and enforcement capacities prior to the merging of the departments into the NYPD. Another detective came from a squad that had investigated traditional crimes, up to and including homicides. Two detectives had served in administrative technical positions and had been responsible for computer applications within their respective offices, and one police officer had been with the HousingPolice and was knowledgeable in telecommunications and telephony.
In 1996, I replaced the lieutenant as the new commanding officer of CITU. My background had been computer operations prior to joining the NYPD, patrol duties in a precinct, and then over a dozen years in the Information Systems Division of the NYPD. My computer experience covered both IBM mainframe technology (systems programmer/manager) as well as PCs. I had received a master’s in management engineering from the Computer Science Department in the CW Post Campus of Long Island University, where I have been instructing since my retirement from the NYPD in 2000. During my tenure with the unit, I was the only person who actually coded to any degree.
The unit, in theory, was and is responsible formeeting the cybercrime needs for the entire NYPD, and thereby the entire City of New York. The police department is a small army of approximately 35,000 to 40,000 members, and the city has upwards of 8 million daytime residents, any of whom can be a victim or a subject of an investigation. Businesses range from small operations all the way up to major industries, such as banking institutions, investment firms, and service organizations.
Although your situation is probably nowhere as large and diverse, hopefully the rationale for including the background of members in the unit will become apparent, because I believe the problems I encountered are typical of many departments looking to establish and maintain such units.
III.Investigations
A.Responsibility
The overall responsibility for the investigation will be delineated in the mission statement and should be promulgated as policy. As stated earlier, selection of the responsible investigatory unit depends on the nature of the investigation and is concerned primarily with agency participation level (interagency, or where the agency itself is the subject of the investigation); the ability to further the investigation; and the need to preserve and present the evidence. Other factors, such as special expertisewith either the victim or the offender, may also shift primary responsibility of the investigation. This bears on the utilization of resources.
Based on my experiences and in speaking with others in the field, investigations that can be conducted by otherunits with expertise from the cybercrime unit should be handled by the other unit. Handling investigations uses up resources: If your resources are better utilized pursing other investigations that cannot be handled by other units, allow the other unit tohandle the investigation. The argument can be made that the case is developed by the cyber unit’s lab team, or by submission of a subpoena; however, this often is simply an assistance function.
Investigation referrals can be taken when your investigatorsare required to substantially devote time and effort in substantiating the crime, locating the perpetrator, obtaining the digital evidence, and presenting it to judge and jury. Referrals can also be taken when most of the case cannot be pursued or furthered by another unit.
The tendency, especially in fledgling units, might be to grab all the cases it can. Bear in mind that the unit’s resources are expended on these cases and may be better applied in actively pursuing those crimes that others cannot.
B.Proactive versus Reactive
Which type of investigation should a unit pursue? The answer lies in the needs of the agency, as well as in the philosophy of the unit’s mission. Many units feel that they wish to have proactive investigations. One type of investigation is that of an online chat for luring pedophiles, resulting in a date or exchange of e-mails, possibly including child pornography. Aside from the immediate aspects of possibly preventing harm to minors, oftentimes the act of catching someone in the act of attempting to meeta minor (albeit a pretend minor) will clear many prior cases of actual meetings.
In determining the investigations to pursue despite their start, remember that, because of the technology involved, the subject of an investigation probably will not reside inyour jurisdiction. In those cases, your unit must refer the investigation to the other jurisdiction. There is another possibility: engaging the target of the investigation to appear in your jurisdiction, or issuing a warrant with the prospect of a protracted legal battle to bring him back to your jurisdiction.
It is up to the unit’s leader to determine the balance of resources in pursuing the investigation and the potential return on the investment of resources. Although a target might be located for an online harassment (misdemeanor), the likelihood of obtaining an arrest warrant and extradition are extremely slim.
Another aspect of the proactive case is the amount of_time_it consumes: both in total hours and in the time of day or day of week. For example,an investigator enters a chatroom pretending to be a minor. Eventually a conversation with an alleged adult occurs during which the investigator feels that this adult may try to entice the minor to perform sexual acts, either over the Internet or to meetIRL (in real life). The amount of time devoted to this online relationship can vary from minutes to potentially weeks. During this period, either a crime has occurred or will occur, or no crime is likely to occur. Hopefully, it has been determined that thesubject resides in, or will travel to, your jurisdiction.
In addition to the total man-hours spent, the scattering of these man-hours across the calendar may wreak havoc with personnel issues: a continuation of a conversation might occur when the investigator is normally on RDO (regular day off) or has not reported for duty (tour changes may be problematic according to contract rules).
The unit will also need to consider having someone available, either within or on loan, for those occasions in which the subject wants to speak on the phone with the minor or expects to see someone young at a meeting location, such as a mall.
Property and theft cases may involve resources. A controlled delivery requires a team of people to handle the delivery, the subsequentarrest, and the inventory of goods that may be present.
A shipment to a hub of a parcel service will require that surveillance be posted because pickup may only be done during business hours and not by appointment. Our unit had several instances in which the target claimed he was going to pick up a package and failed to show, as our team was on the set. Although this is not different from the noncyber investigation, consider the effect it might have on the work if your lab rats had to man the surveillance as well.
C.Productivity and Metrics
Understand how the performance of the unit and the commander will be measured. Although the work performed is different, in all likelihood the simplest manner in which to measure productivity already exists within the organization. Often they devolve down to caseload, case clearance rate, and monetary overtime.
The bottom line is that unless you manage to persuade the administrative powers-that-be otherwise, your unit (the round peg) will have to fit into the typical unit’s model (square hole). Most often, the peg is hammered until it fits the square hole.
Determine whether the metric model imposed is real: If not, convince the administration that the model is not feasible, possibly for some of the reasons listed in this chapter.
One unspoken measure of productivity ispress time. This has to do with public perception and notice of the unit’s efforts by the administration. For this reason many units’ leaders might appear to be headline hungry. The truth of the matter is that resources might increase due to positive press.
D.Resources
Dependent upon the nature of the investigations that the unit’s mandate includes, resources need to be available. It is up to the manager to provide those resources. More importantly, it is theadministration’s responsibility to appreciate and support the need to supply the_proper_resources, such as the following:
Staff
Equipment and supplies
Time
Money
Outsourced expertise
Unlike many other units, simple numbers do not equate to manpower. As stated, because of the various aspects of the technology involved, one staff member cannot simply replace another. Temporary assignments from other units may not alleviate many tasks otherwise performed by unit members. Conversely, do not hesitate to utilize personnel for the purposes of observations, stakeouts, canvassing, or administrative trivia such as filing or the processing of property and evidence.
Purchase of equipment is essential. What is unfortunately not so obvious is that the manner in which procurement occurs requires careful handling of budgetary issues.
If requested to submit a plan for purchase of equipment and supplies, realize that it may be difficult to project what equipment will be needed. Often the reason for this difficulty resides in the fact that the technology either currently does not exist, or is in development. Requesting funding for unknown quantities of nonexistent products is difficult, and increasingly soas the budget projection window extends into the future. Short-term concerns are even difficult to predict because Moore’s law (predicting the lifespan of computer technology) has shrunk to about half a year.
If your agency allows for_discretionary_or_inve__stigative_funds, this may allow for some leeway in case of emergency. For example, setting up a lineup may require nominal fees to participants in the lineup, or travel expenses, or other costs incurred during the investigation. As long as these costs areaccounted for, hopefully you will be in accordance with policy.
In the event that the fund is based on a grant supplied by another agency (federal or state), the account will certainly have oversight. Emergency purchases of equipment or supplies in order to conduct an investigation will be red-flagged. Proof of expenditure will be required; this means that, should you require a new peripheral that just hit the market in order to process evidence, or even the recording medium for the device, you must accountfor it. The device should not make its way into someone else’s office.
Another means of obtaining equipment is through forfeiture. Typically your organization might decide that, pursuant to an arrest, part of the adjudication and penalty will be forfeiture of the equipment owned or used in the commission of the crime (e.g., a pedophile using a computer to chat online with children).
Although this is certainly one way of obtaining equipment, I tend to advise against it for two major reasons: (1) you avoid the appearance of impropriety (arresting solely to get equipment); and (2) by the time the equipment goes through the forfeiture process, even if the equipment is what you can use currently, Moore’s law kicks in, and you might have obsolete equipment, subjecting you to reason 1.
In terms of time, how much do you have? How much do you need to devote? Cases languish for the simple reasonof time. Often we do not have the ability to devote enough resources to a particular investigation in order to accomplish all we need in a timely manner. Time constraints require that we devote more man-hours to ensure that all the tasks are done.
Conversely, you need to ensure that you have the man-hours to throw into the problem. As stated earlier, the interchangeability of personnel is no longer true once technology enters the equation. Specifically, the skills required mean that a_particular_member’s hours be devoted to the problem at hand. Unfortunately, this may not always be possible because of overtime constraints. As stated earlier, overtime issues can be touchy, both from the union perspective as well as from the administration’s point of view. Contractual agreement may entitle that the member incurring the overtime elect the method of payment in cash or time. Administration would prefer time because in normal cases 1 man-hour can be replaced by another man-hour. This is not necessarily true in technical cases. Justification can be made by comparing your replacement’s value to those of similar cases. Administration could probably appreciate better the argument that replacing a lab examiner with a programmer from the other division is comparable to having the police lab fingerprint technician process DNA evidence.
Accrual of overtime is closely reviewed due to possible abuse (aside from exceeding budgeted projections). It is quite possible that the closer to retirement a person is, the closer the scrutiny will be, because the pension is likely based on monies earned in the last year or so.
One year I had two unit detectives exceed cash overtime earnings. One exceeded earnings as he was performing essential lab work that could not be deferred (on a sensational murder case, among others). The other detective had been called out on a prolonged detail because of his diplomat training (protective services, etc.) for United Nations duty. Despite my protests that the overtime accrued on the UN detail would count in overtime totals, I was told that, because the monies came from another budget line, they would not count. Cynic that I am, I was not convinced. Sad to say, I was proven correct.
The result was that I was called to task for allowing these members to accrue overtime (out of 40,000 members they made the top 50 list). Despite accounting for every minute of their time and relating it to required and time-constrained essential tasks that could not be performed by other members, both members were enjoined from performing cash overtime for the next 6 months. The inability to use their skills then required attempting to replace those hours with another member’s hours (hopefully qualified). This had the unfortunate effect of pushing back tasks the other membershad been working on. A secondary effect was that evaluations (and possibly allocation of resources) may be dependent upon the strict liability of violating policy.
The point is not any unfairness but rather that, due to bureaucratic inertia, considerationneeds to be given to balancing work, time, and resources_capable_of doing that work. Rather than looking at incidents such as this as hammering the nail that sticks out, administration should consider this an indicator that additional resources (or less work performed) are required.
IV.Staffing
Depending on the mission, staffing considerations can vary widely:
Functions
Investigate, assist others, or both
Field investigations
Lab investigations (examinations)
Provide testimony
Degree to which unit is committed to assisting other units or agencies
Nonmission tasks and responsibilities
Is the need for sworn personnel to perform lab functions critical?
Can you recruit the appropriate personnel into the unit?
Identification of personnel
Civil service constraints
Motivators
Longevity and retention
Cost per member
Interchangeability factor
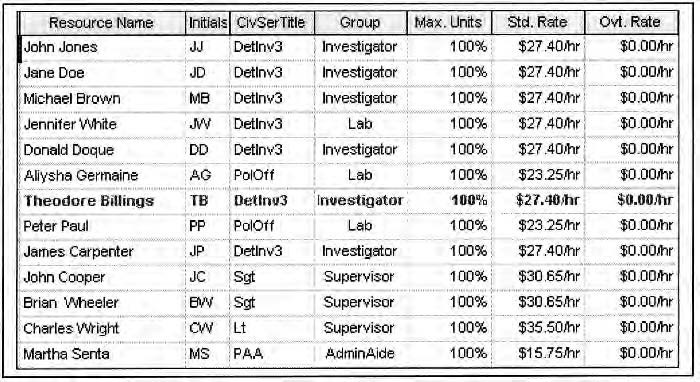
Figure 2.1Staffing list for a nonspecialized unit.
Field investigations_ideally_should be conducted separately from lab examinations. I am stating the ideal, but, unfortunately, reality sometimes dictates that the same personnel who perform the examinations of the digital evidence also conduct field investigations. As I will discuss, this approach is counterproductive in more that just one aspect.
Figure 2.1 lists the staffing for a nonspecialized unit. The staff includes a lieutenant (commanding officer principal administrative side), two sergeants (supervisors), detective investigators, police officers, and administrative assistant (PAA).
We will examine different scenarios that utilize this staffing arrangement and determine the pros and cons of the different schemes.
The assumptions we make are the following: Lieutenants, sergeants, detectives, and police officers are sworn or uniformed members of the service, and the forensic specialist and PAA are civilian members. The workweek is approximately 43.5 hours for the uniformed personnel and 40 hours for civilian members (FLSA notwithstanding). The reason for this imposition is that accrual of time in excess of the weekly limit results in paying of overtime. Within the NYPD, uniformed members (below the rank of captain) have the negotiated option of taking overtime in cash, or in time. The decision is_not_mandated by supervision but rather isat the discretion of the employee. Technically, if the employee is ordered to perform a duty and elects not to accept the time option, then cash overtime must be paid.
Tours of duty are weekdays and span the day and evening hours; personnel do not performscheduled tours on the late tour (midnights) or weekends normally.
Consider the following scenarios in utilizing personnel:
Uniformed members performing dual roles
Investigator
Lab technician
Uniformed members specializing
Detectives investigate
Police officers function as technicians
Specialization including civilian members
Detectives investigate
Police officers as technicians
Supplement investigative effort
Civilian technicians
Outsourcing of technical assignments and duties
A Gantt chart quickly demonstrates the times and resources involved in a typical project. A precinct detective unit forwards a complaint of a minor being involved in an online chat. The parents obviously are concerned regarding the possibility of the child having met an adult online.
The receipt of the complaint occurs late on a Friday, leading to an interview of the minor and family on the following Monday. The reason for the delay is the Monday-through-Friday nature of the unit.
On Monday the_catching_detective (Ted Billings) and his partner interview the minor and the family regarding this complaint. They obtain consent for seizure and examination of the computer. Billings removes the computer along with other materials in preparation of the examination.
At this point in the investigation personnel assignments can proceed in a variety of ways. Possibilities include:
The case investigator performing the investigation
Another lab specialist, sworn member performing the examination (detective or police officer)
A civilian specialist performing the examination
A.Case Investigator
The investigator is familiar with the case and has the knowledge to recognize any pertinent information that might be contained in the digital evidence. This could be construed as an argument to allow the case investigator to examine the digital evidence. Whether or not this logic applies is at the heart of the question as to whether or not the unit should be specialized. Should the case investigator also conduct the lab exam of the digital evidence? That depends on contract and civil service regulations, available resources, as well as other human-resources-type matters. Case investigators may wish to perform lab functions for a variety of reasons, such as job enrichment, maintaining control of their investigation, or acquiring skills in order to increase their market value.
Although an argument can be made for the investigator searching the digital evidence for information germane to his case, each investigator carries a caseload of several, if not tens, of cases. Typically, we can assume that each investigator might be carrying a caseload of a dozen open cases. The reality is that in a typical detective squad the number is much higher; however, in a unit handling a_specific_subset of investigations, the number may be around a dozen, depending upon total manpower.
The prime purpose of the investigator is to investigate. If the fear of not finding relevant digital information is of concern, then the investigator must spend time conferring with the examiner and reprocess the evidence, if required.
If we draw a parallel to cases that require forensic accounting, the investigator_communicates_to the specialist what he is looking for and discusses the results with the specialist. In a similar fashion, the lab tech can search for the information and communicate the results to the detective. If one argues that the investigator is required to also search the digital evidence, then perhaps by extension it might apply to having the_prosecutor_search the digital evidence because it might contain something that only_he_will pick out.
What_is_the advantage then of having the investigator perform the analysis of the evidence? The possibility that the investigator will recognize pertinent information that might affect the case in a more timely fashion is probably the first consideration. By removing the turnaround time of communicating with the examiner, the timeline may be shortened.
The downside to the usage of the case investigator is that the investigatorneeds to be versed in the usage of the tools used in securing and analyzing the evidence. In order to remain current, the investigator now needs to be trained in new technologies. In short, he has less time to pursue the actual investigative side of a case.
B.Lab Specialist
The lab specialist has the training and ability to safeguard and search the digital evidence for any information the case detective might require. In doing so, the lab specialist can free up the investigator in order that he or she might pursue another case. In Figure 2.1, I presented a staff composed of all sworn uniformed members (with the exception of the administrative aide). Some of these members are assigned to the Lab group. Ideally, members of this group will process evidence and prepare reports for the investigative staff. These technicians should ideally report to a different supervisor than the investigative staff; however, unless the agency is a large one, there may be only one supervisor. In that event, the supervisor shouldstrive to keep the two groups separate as far as duties are concerned.
The benefits of allowing specialists to process the evidence are that fewer people need to be trained in certain disciplines. Investigators have more time to devote to the investigation and the “shoe leather” aspects of the case. Additionally, because these people specialize in processing evidence, it is easier to substantiate them as qualified subject-matter experts, (SMEs); partially, this is attributed to sheer volume of work product. The fact that the people in this group routinely process evidence and write lab reports means that the consistency of the work product should be better ensured, and the amount of supervision regarding their training and monitoring may decrease.
There might be practical issues in utilizing uniformed personnel as lab technicians; for example, you run the risk of having them removed for details (parades, riots, public events, etc.). The other possibility is that civil service regulations may rear up and preclude a noninvestigator from working on evidence, because this might be deemed an investigatory function. This needs to be determined in each individual agency.
By replacing the uniformed specialist with a civilian specialist, potentially, the uniform member is freed up to pursue other duties, either within the cyber unit, or outside. Different agencies may restrict the scope of civilian availability in terms of working hours. If this problem exists, realize that oftentimes evidence needs to be recovered andsafeguarded (preferably by a uniformed member) and examined at odd hours or on civilian holidays.
Can we alleviate all our problems if we use civilian lab technicians? In all likelihood, you will probably still have some problems. In some respects, getting the proper civilian staff may be more difficult than recruiting and retaining a uniformed staff. In large part, this depends on civil service law.
Recovering evidence may require instances in which the recovery is at the scene of a homicide; most would agree that it is preferable to send in a uniformed person to handle this evidence. This does not preclude using civilian lab technicians but simply means that a procedure be developed to allow uniformed first responders to perform seizures in the field.
C.Simple Case: Dual Role
In this scenario, a complaint arrives at the unit regarding a conversation alleged to have taken place between a 12-year-old and an adult. The conversation is suggestive in nature, and the parents are concerned that the child is being lured online. The child and parents need to be interviewed, and consent must be secured for examination of the computer and related materials. While interviewing, the case detective catches another case involving a
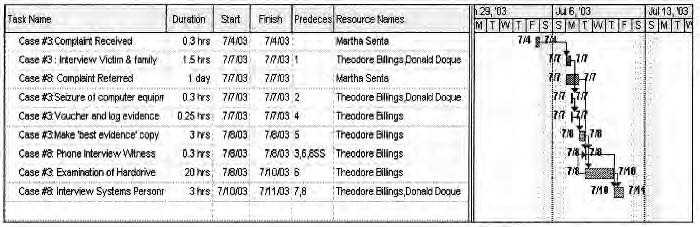
Figure 2.2Gantt chart for Detective Billings’s tasks.
corporation. The corporate case involves a computer trespass and may also involve loss of corporate data and breach of confidentiality (of clients and corporate information). The initial corporate case interviewmay be conducted via telephone. Detective Billings determines that he requires speaking with corporation personnel subsequent to the telephone interview, and he sets up an appointment.
The Gantt chart in Figure 2.2 focuses on Detective Billings’s tasks only insofar as the two cases are involved.
Taking into account Figure 2.2, we can determine that the start times of the tasks performed by Detective Billings are delayed. The nature of the tasks can additionally be constrained by depending on a prior task’sending (finishstart dependency). Not all tasks are of this nature because there are some tasks that may run in parallel, or may even interrupt other tasks.
An example of a task that might run in parallel is a telephone interview with the hacked corporationwhile Detective Billings is processing the copy process and has some downtime.
A Gantt chart is useful to visually present resource usage and map it against a calendar. If properly formulated, the information can yield a critical path that indicates thosetasks forming a chain; a delay in this path will push back a completion date. A delay in another task may alter the critical path, so that a different chain or set of tasks now is the critical path. A chain would consist of the following tasks:
Seizure and securing of evidence
Purchase and installation of hardware or software to process evidence
Analysis of evidence
Report of results
Investigator actions
All things being equal, if the acquisition of some critical component required to process the evidence is delayed, the entire project is delayed.
Should the lab examiner be incapable of processing the evidence (exigent case), the start of the analysis taskis pushed back, thereby delaying the project. If the analysis needs to be performed by a particular member, and due to a temporary assignment he is not available, barring replacement, the entire project is delayed.
In this example, if Detective Billings is replaced by a lab technician at the Best Evidence Copy task, then he is freed up to pursue other leads or initiate new cases.
D.Participation with Other Agencies
This is potentially one method in which to fast-start an operation. By joining part of a task force, you can leverage the existing structure of that team and develop personnel with expertise. If your agency is not large enough to sustain its own cyber unit, this is one method of proceeding.
This approach is recommended for many agencies; it allows the sharing of resources, intelligence data, and networking to other agencies with the appropriate resources, should the need arise.
One reason to consider setting up your own unit is the expected inability of the task force to adequately process the nature or the volume of the work your agency expects to handle.
The cost effectiveness of training your own personnel may also be prohibitive; task forces may provide training, because they may be funded precisely for this purpose.
The other aspect has to dowith retention of personnel. Although I will not quote Herzberg et al. regarding job motivators, it can be expected that properly trained personnel may have a limited life expectancy, because of their marketability in the private sector. The task force participation can better (although not positively) assure individual agencies that there will be a cadre of trained personnel to handle work.
E.Civil Service: Performing Out-of-Title
Assignment of personnel to tasks is complicated by the requirement to ensure that personnel function within the scope of their civil service title. Allowing an employee to perform duties on any regular basis lays the groundwork for that employee to sue for that title. Needless to say, the administration would take a rather dim view of this because it violates several administrative policies: budgeting, resource allocation, and force counts, to name a few.
F.Recruitment, Hiring, and Retention
The ability to locate and then to hire the appropriate personnel can be challenging. Because the base pay of the member does not increase, different motivators must be found to bring proper personnel into the fold of the unit. If members stand to lose overtime pay, or shift differential pay, these may bedemotivators.
Locate members who possess the skills appropriate to the mission, and determine the trainability of those potential candidates.
Uniformed members can be sought and recruited from other units; however, often the other unit will be opposed to the move.
There is a different set of issues involved in recruiting civilian personnel. If you cannot recruit from within your agency, there might be new hires from a standing civil service list. If you are assigned a civilian on a provisional basis, because there is no officially promulgated list, then be aware that this person may have his or her position relinquished pursuant to a publishing of the official list. If that personwould have been hired, you_might_be able to keep him. On the other hand, if there are persons who should have been hired before your civilian, you may lose him or her and pick up an unknown person.
Unlike other jobs, in which pay can be tied to performance, civil service often fails in its ability to recognize and reward employees monetarily. This may have effects on retention as well as initial recruitment into the unit, whether the member is uniformed or civilian.
G.Administrative Issues
Overtime pay and time limits may have a bearing on all aspects of staffing, from initially recruiting people to keeping them. Although studies conducted cite that pay is not a motivator, the same studies cite that_lack of pay_can be a demotivator. In essence, civil service pays the same base pay according to rank. If someone is assured of making more in a current assignment, he or she will be less inclined to accept an assignment in which the likelihood of reduced income exists. The perception is of losing pay rather than of going back to base pay. As will be related, pay issues also have a bearing on the operational aspects of the unit.
Regardless of the success or failure of the unit commander in recruitment and selection of the team, one inescapable fact remains: Longevity of the individuals as part of the team will remain a serious factor in maintaining the viability of the unit.
H.Retirement
Despite any writings to the contrary, my belief is that the majority ofthe sworn personnel will probably leave at the first opportunity, if not sooner. For example, the NYPD retirement currently calls for a retirement with half-pay pension after 20 years of service. Vesting out allows the uniformed member to retire after only 15 years of service with a reduced pension. In both cases, the pension payments start on the twentieth anniversary of joining the department.
The reason for many uniformed members remaining over 20 years is that many might not match the pay on the outside, as well as the benefits enjoyed by the membership (unlimited sick time, 5 weeks annual vacation, and tax-free pensions in the case of serious line-of-duty injury). For others, the police culture is the reason to stay with the job.
In general, any personwith a marketable skill may seek employment on the outside. The overwhelming reason for this is twofold: pension considerations as well as the immediacy of a higher paycheck in the private sector.
I.Advancement and Rewarding
In the event that the workplace is dictated by civil service regulations, it is inevitable that the very system that helps avoid job inequities and abuses will tend to work against performing a particular job.
Because civil servants do not receive annual bonuses based on performance,the mechanism for people to advance in pay scale is either to recognize service time contractually, receive special-duty pay grade, obtain a designated rank, or seek a promotion in civil service rank.
_Aging out_refers to any pay increase accorded to thoseemployees who have attained a certain level of years on the job. Generally, this is a nominal amount of money that most people would consider nice, but not a deciding factor by any means in remaining in that job.
Many agencies offer a skills pay increase if the skill is required as part of the job. One example would be the ability to pay someone a premium for fluency in a language if that person is called on to use that skill. Unfortunately, many unions will not pursue this avenue during negotiations.
Designated rank is awarded, and with it comes an increase in pay. The rank is not protected by civil service law: In essence, the member serves at the pleasure of the commissioner or chief of the department. The rank is_banded_within the range of a base civil service rank. In the NYPD, the base rank of police officer had various designated ranks associated with it: police officer special assignment (possibly defunct), detective specialist, detective 3rd, detective 2nd,and detective 1st. The grades for detective increase in pay from 3rd to 1st, and the specialist is a noninvestigative title. Likewise, there are designated ranks for sergeant as well as lieutenant. For the ranks of captain and above, the base civil servicerank is captain, with all others being designated as ranks. Obviously, there are many more rules; for the sake of this chapter we will not explore them.
The limitation of awarding a designated rank will cap the amount of money that personnel may receive in salary. Other considerations, while allowing the employee to earn more over the year, will actually increase the number of tours of duty to be performed, as well as potentially impact the employee negatively in other ways.
1.**Unavailability of Personnel and the
Interchangeable Man
The nature of any job may make personnel unavailable for prolonged periods of time. Unfortunately, it is a fact of life on the job, and managers must deal with it. Some of the reasons might be:
Medical leave for being sick
Transfer to another assignment
Promotion
Suspension or other limitation of duty
Details or special services
In general, you may still be carrying the person on the roll call; however, as far as the administration is concerned, your manpower is based on the total roster count.
Part and parcel with the job is the attitude (both by the officer and administration) that the average officer, by and large, is capable of being productive across a wide and disparate range of work environments. My opinion is that administration perpetuates this myth — they grew through the same culture.
In fact, normally dropping an officer cold into a new environment can work out, and most officers perform well when assigned new tasks as long as they are given the parameters and expectations of that task.
Although it might seem obvious that a person lacking computer skills should not be in a unit in which these skills are required, from firsthand experience I can attest to the fact that many assignments aremade simply because a department needed a body, and the administration had a body to give you. (The often unsaid reason might be “we have no other place to put him.”)
The normal assignment for people of this category might be clerical in nature, because they are often on extended medical limitations or bounced from patrol or investigative duties.
The other problem is that for civil service reasons (and department policy) you may be prohibited from utilizing that person in an investigative capacity, either due to the limited nature of their current status or to problems with utilizing someone in tasks not within the scope of their civil service title.
If you are the administrator who has assigned this person to the unit, it might_not_be a favor from several perspectives: (a) The person may be incapable of handling mission-critical tasks; (b) the person may be unable to conduct routine tasks; and (c) the administrative decision to assign a possible problem child not only fails to alleviate the unit’s everyday concerns but in fact exacerbates them.
If you are not privy to police culture and responsibility, here is a simple example: As a supervisor on a parade detail, you are issued 10 “bodies” for the duration of the parade. Each of these people has come to the parade on their own, in uniform, and the first time you have ever laid eyes on them is at the site. One of these people is not in the uniform of the day, or otherwise has decided to adorn his uniform. This renders him no longer uniform with the others. Someone higher than you in rank decides on a vicarious lesson, and issues a rip to the offender, and then one to_you_for failing to supervise. Although this is a stretch, unfortunately it does happen, and serves to illustrate the notion of strict liability vis-à-vis the responsibility of the police manager. If you extrapolate this scenario to assigning a person with diminished capabilities, although you might incur agency repercussions, the worth of that person is in question if you were to take a benefits-to-liability ratio.
The process of helping out the cybercrime unit with the addition of nontechnical, untrained, unusable bodies other than for menial work is not necessarily beneficial. Combined with the fact that such people might have been placed there because nobody else could use them, or that they’ve gotten into trouble elsewhere, their presence is detrimental.
Routinely the interchangeable-man factor rears its ugly head in the other direction. For example, each September the United Nations requires that many diplomat-trained officers (typically detectives or supervisors) are assigned to that temporary duty. Thatperson is essentially lost to the unit for that duration of time. Any other work to be done by this person cannot be performed while this person is loaned out. This becomes an issue for the following reasons:
Your manpower count remains the same, even though your manpower is reduced in reality.
These assignments are done on a fair basis (spread out over commands) in order not to impact any one command inordinately.
This member may accrue overtime in the outside assignment.
Any replacement body is not trulya replacement unless the member loaned only performs menial tasks and not mission-critical ones.
Tasks assigned to this member may languish awaiting his or her return, or if time-sensitive in nature, may have to be assigned to other members who, in turn,have their own time-sensitive tasks piling up.
If you were to examine a Gantt chart based on these circumstances, you would quickly see the effects of detail assignments. The bodies-to-work ratio must be maintained so that overtime is allocated to those members having to pick up the slack. The payment of cash overtime results in administrative oversight headaches, in which the commander (as well as_his_commander, and_his_commander and so on up the chain of command) is required to justify the expenditure of_cash_overtime and then explain how this will not occur in the future. This is definitely a sticky topic because such overtime may be used as a productivity measure of both the unit and the leader.
J.Misuse of Personnel
Perhaps the term instead ofmisuse_should be_inappropriate utilization of human resources. In any event, it covers the gamut from out-of-title assignments to favors.
To some degree, I have already mentioned utilizing people outside the scope of their title assignments. Specifically, a policeofficer is a noninvestigative member. Using this person in the capacity of an investigator for a prolonged period of time may result in an unintentional promotion, depending on civil service law and union contracts. For various reasons, this plays havoc immediately with the supervisor or commanding officer and subsequently the effect percolates upwards in the chain of command. The supervisor should be aware of the need to contain (without permission) the extent to which people conduct tasks outside their titles. The immediate issue is that this demonstrates to management a lack of control, and secondarily (perhaps more importantly) budget issues ensue as well as command strength and manpower issues.
The command strength deals with the assignment and distribution of personnel throughout the department. The assignment also brings into play the financial resources dedicated to any particular unit. In the NYPD, units are assigned to divisions, and divisions fall within bureaus. Each bureau is allocated a budget,and lines within that budget. Needless to say, once a budget is impacted, accountability for changes in that budget can reverberate throughout the command structure. The manager should be aware of the budgeting within his or her own command, and how it derives from the parent command and so on. Failure to contend with these issues results in the inability to plead for required resources.
The entire department’s command strength is a count of members in ranks. Budgeting is predicated on the command strength; therefore, when these numbers are skewed inadvertently, someone_will_notice.
It is inevitable that at some time or another, resources of the unit will be requested to provide services for other units. These favors can range from setting up someone’s desktop computer, to setting up a PowerPoint demonstration, to writing an application.
If your agency already has a unit tasked for these purposes, then why is your cyber unit being asked to provide this service? In all likelihood, the answer is confidentiality, control, and determination of the work. You need to determine whether the latitude of the mission statement covers such incidents. Just as elsewhere, refusal to perform these tasks is difficult because the work can be ordered. Inevitably, the decision to do these favors, whether ordered or not, is a political one; a favor delivered may be a future favor to be returned. Conversely, a favor denied, may be a future request denied.
K.Interviewing
The supervisor of the unit, aside from having the “basic promoted upward through the ranks” managerial skills should also have knowledge of project management skills. The issues involved in staffing and maintaining such a unit requires a working knowledgeand understanding of the underlying technologies.
A major obstacle in staffing a unit is in the initial determination of a person’s suitability to the task. The pool from which a manager draws available personnel is very shallow, and not very wide. Unfortunately, this often leads to settling for a candidate who might not be a good fit.
Having reviewed the potential areas that members might be working in, consider evaluating the current skill set as well as the_trainability_of that person. As stated earlier, all or some of these skills may be required in aunit, and all or some of these skills may be embodied in the same individual:
Programming
Examination of target machine (scripts, code)
Ad hoc queries using standard office suite tools
Homegrown solutions requiring coding
Forensic specialist
Operating system and hardware familiarity
Mechanic functions (backing up, evidence copy, acquisition of data)
Ad hoc queries using standard office suite tools
Patterning (recognition of the unusual)
Versed in forensic tool kit(s)
Network skills
Digital evidence
Investigator
Technology overview
Network basics
Digital evidence first responder skills
Supervisor
Working knowledge of law pertinent to cybercrime issues
Investigation supervision skills
Technology supervision skills
Project management skills
If you are in need of programmers either to write original code, or merely to interpret code on target systems, the first obvious choice is to solicit from within the organization for members currently functioning in that capacity. If your organization isnot large enough to support a staff of information systems or MIS personnel, then other avenues must be explored. If your department does have such staff, the ability to draw from that staff may be impeded by ongoing projects that require a particular person to remain within their unit. Managers are extremely loath to release resources from their grasp; any resources that are easily obtained should be reevaluated. It is possible that members released with little fuss have been labeled problem children or have been of little value to the other manager. In other words, sometimes a donated employee should be subjected to closer scrutiny.
If your department or agency is small and does not have a standing force from which to draw, and you require a programmer type or a member having some programming background, then you have other options: (a) examine the benefits of utilizing another agency’s personnel (task force, or loaner) and if this is not feasible then (b) search for an internal resource.
As stated earlier,joining forces with another agency is feasible and has the additional benefit of not costing your department training dollars. The downside is that, although you might require the work to be processed in a very short time frame, you are now subject to theother unit’s workflow. Any task relying on completion of this initiative will be deferred as an external process becomes part of your critical path.
The other unspoken argument is that a quid pro quo might exist, and that cost may be prohibitive. Sharingwork with another agency can result in sharing any benefits. These benefits may extend to resources, sharing a headline, or even not being_in_the headline when the news breaks. For various reasons, public notice is actively sought by many agencies. One reason may be personal gain in building up a curriculum vitae for advancement or retirement. Other reasons might be to ensure that an elected or appointed public official is perceived favorably. If resources are required, then attempting to obtain a grant orshare of budgeting may be another reason for pursuing headlines. The other reason is simply to fulfill one of the police functions, to provide a sense of public security.
Looking for an existing resource can be easily done if a database of skills is available. For example, simply search for those with college backgrounds in either information systems or computer science. Additional means involve issuing bulletins for personnel who have those skills and have decided not to notify the department or update their personnel folder. A decade ago, finding such people was difficult, but as time passes more members of your department might have gone through a curriculum involving information technology courses.
If possible, determine whether the person has the appropriate skills. For example, if the person is required to code on a routine basis, consider administering an actual coding test.
Failing to find an existing programmer requires that you identify someone who is trainable. It has been suggested by numerous studies, and empirical evidence leads many to believe, that math skills are one predictor of coding capability (due to the level of abstract thinking required). Because there are few math or physics majors around police departments today, you can refer to theSAT or ACT math score as the best available source.
A lab technician used to be the person who was locked away in a cubicle, and once a week a pizza was slid under the door. Realize that the lab technician, as well as the investigator, will author reportsand be called on to testify. If offered a choice between equally (technically) competent people, consider those possessing strong verbal and written skills.
L.Training
Determine basic skill set of investigator and lab examiner
Identify target skill set
- Quantify member count possessing skills required by unit
Training regimen
Time
Budget
Training coverage
Geographic
Temporal
Personnel
Identification of immediate and future training
Scheduled
Attrition
Other nonavailability of personnel
I am not a believer of leaving the obvious unstated. Training of personnel iscritical. Depending on the philosophy of whether or not accreditation or certification is required, accordingly the training curriculum must match that desire and monies allocated toward that end.
A common failure is often seen in an agency providing initial training and subsequently failing to provide additional training. The need for ongoing training is essential due to the ever-changing nature of the technologies involved.
Manypeople feel the need for certification, such as a Cisco-certified examiner. The opinions on this aspect of certification vary. Although it might be desirable to have a person certified on Cisco equipment (or other vendor), it may not be essential. Certification assumes that a person has completed a course of study and indicates that a person has passed a test and is deemed as certified by that organization. This can be a nice shortcut when providing testimony. Establishing someone as an expert witness, however, does not require that he or she be certified.
The additional aspect is that certification applies to the technology existing at the time of the certification. As indicated earlier, time and technology wait for no man. If certification is a goal, thenconstant training and certification is required. The alternative is justifying to defense counsel how the examiner is an SME on equipment or technology developed_after_his certification.
Another method of obtaining certification is to get assistance during the course of the investigation. Alternatively, it is permissible to write SMEs into a search warrant.
Substantiation of expertise is the aim of the prosecution. Your aim should be to ensure that you can provide that substantiation, either through formaltraining, accreditation, participating in investigations, prior experience, or other avenues proving knowledge to the level of SME in the field. Bear in mind that defense counsel will attempt to attack the SME status of the investigator or examiner.
Training opportunities_do_exist for law enforcement personnel. The High Technology Crime Investigation Association (HTCIA) has local chapters that sponsor meetings. HTCIA meetings attract law enforcement as well as their public sector counterparts and academia.Generally, topics of current interest are presented, allowing members to obtain valuable knowledge. The other aspect that cannot be downplayed is the networking aspect. Attendance will allow investigators to meet other investigators in the field. The ability to contact others who have faced the same problems is invaluable. Some of these organizations sponsor annual conferences, during which time presenters offer information or demonstrations normally not seen by investigators. Often the attendance is at areduced rate for those in government, or they offer sessions open only to those in law enforcement.
The National White Collar Crime Center provides training for law enforcement, and the cost to the agency is simply the transportation and the feeding of themembers attending. Housed in Morgantown, West Virginia, this organization started by providing training such as basic data recovery in their facilities and has since expanded their operations both in terms of curricula as well as venues where they offer the courses. Much of the training is the result of a group that met several times a year and was composed of representatives from many law enforcement agencies from federal to local levels as well as corporate and academic representatives.
The Federal Law Enforcement Training Center (FLETC) also provides training opportunities. Their center in Georgia provides training sessions for law enforcement.
Universities are starting to offer courses in computer forensics and network security issues. One of these is the University of New Haven in Connecticut and its branch in California. One problem an administration may have is sending a member for training to a class in a university setting that offers credits for attendance. My suggestion is that administrations balance the possible perception of any impropriety in getting college credits.
Oftentimes, the private sector is willing to make available seats at in-house classes for their own personnel. Finding out about them is the problem, but joining organizations suchat the HTCIA or others may allow contacts to be made whereby your organization is made aware of such training, or such training is created specifically for the public sector by the private sector.
The training paradigm offered by many of the federally sponsored training seminars and classes often has been at odds with the ability of the units in the state and local police agencies. Generally, the sessions offered were of 1 week’s duration, if not 2 weeks. In speaking with representatives from the agencies’local law enforcement, I was given the impression that their administration would probably not entertain many such training sessions.
Be sure to budget time and money for seats at these sessions. I once budgeted and reserved seats for five members of my staff to travel to an adjoining state for a weeklong training session on securing and analyzing digital evidence. The personnel could all afford to be away for the week; they had no pressing tasks that could not be deferred or performed by other members; and the monies were already allocated to my budget line. However, the request was denied for all five members, and ultimately only two were allowed to travel for the training. The reason given by a gatekeeper in the organization was essentially based on thefact that another unit (the Bomb Squad) was only allowed to send two members for their training. Whether or not you encounter situations such as this depends upon your organization.
What effect did this have? Subsequent budgets must be based on needs and prior budgets. Mandates may slash a budget automatically by 10%, or your budget may be based on the expenditures (not the allocations) of the prior year’s budget. Lastly, if the budget lines are different for training, supplies, capital equipment, and such,transferal of unused funding from one budget line (training) to another (equipment purchase) may be problematic.
Although the surface has been barely scratched, consider carefully the purpose and mission of the unit, and the level of support required to create it, maintain it, and administer it.
Consider also the risks along the way. Attrition of personnel as well as budgeting issues can cripple the unit. Failure to obtain proper training can have deleterious effects. In relating some of my experiences, perhaps you can avoid circumstances that would place you in that situation.
Understand the nature of the agency that controls the unit, as well as those agencies contributing to the unit and their needs. Even in the event that your agency is supplying your personnel to a task force, ensure that youragency’s administration understands the conditions and constraints of these units.
V.Summary
The reader must remember that any consideration for planning and staffing a cyber unit begins with the definition. A clear and concise mission statement will guide and support plans. Failure to provide such a statement can result in duplication of effort, detrimental sharing of resources, or failure to obtain necessary resources in order to fulfill the mission.
Staffing issues such as recruiting and retention differ in many respects from those in the private sector. Not all motivators or demotivators applicable to the private sector necessarily have the same impact in the public sector. Motivators, such as rewarding for performance, do not exist in many public sector agencies or certainly not in the same form if they exist at all. Civil servants are restricted, by law or union regulations, from monetary benefits as seen in the private sector; for example, if the unit had a good year and closed more cases, there isno bonus.
Careful consideration must be given to the selection of and retention of personnel. The recruitment and selection process is constrained by the available candidate pool; furthermore, eligible candidates may not be lured away from their current assignments.
Retention motivators need to be identified. As noted, pay is probably not a viable motivator for retention. Other avenues must be explored and implemented; my suggestion is to ensure that staff has adequate training opportunities. Participationin technical seminars provides motivational opportunity for personal enrichment and growth. Affording the chance to work with current technology is another motivator.
The problem in providing these opportunities is that many managers may view it as hastening the day in which the staff will take leave. The counterargument is twofold: (1) Civil servants are bound by time constraints in terms of retirement and, more importantly, as far as the mission is concerned; and (2) failure to provide adequate trainingwill hamper the unit’s ability to meet the mission, or in fact cause the unit to fail miserably.
Perhaps the most difficult task is for the manager to overcome the reticence or even resistance of the administration in providing funding for training and technology. Every effort should be taken to rationalize the need for training, despite the possibility of staff departure due to training. In many instances, training of the administration is required in order to alert them to the very different nature of a cyber unit, both in staffing and their resource needs.
In essence, we need to remember that the cyber_investigative_unit falls somewhere between the paradigms of public sector law enforcement and private sector information technology teams. Management mustdraw from lessons learned in the private sector and apply those rules, where appropriate, and manage to find methods to overcome the encumbering regulations of the public sector world. In those instances in which we cannot overcome the limitations, management and administration need to realize that oftentimes the only solution is to hope for the best and plan for the worst. This risk analysis identifies the possibilities of retention failure (_one_specific example) and weighs it against the effects of failing to provide that training (which may very well lead to a staff member leaving), causing the mission to fail.
| Criminal Investigation Analysis and Behavior: | 3 |
|---|---|

WILLIAM L. TAFOYA
In the 1982 sci-fi movieBlade Runner, Rick Deckard (Harrison Ford) is responsible for locating humanoids that escape from an off-world mining colony and, as stowaways, return — illegally — to Earth. Set in the year 2019 in Los Angeles, Blade Runners (detectives) are answerable for tracking down and “retiring” these so-called Replicants. Early in the movie there is a scene wherein technology and clever interviewing are combined in the investigative process to determine whether the suspect is indeed a replicant. As the person is questioned, useis made of a device reminiscent of a twentieth-century ophthalmology instrument employed to measure glaucoma. The suspect’s eyes are examined as emotionally charged questions are posed. This proactive technique is undertaken to provoke a psychological response (rage) calculated to generate the physiological reaction of dramatic and sudden pupil enlargement (Roy). The hard sciences have already been integrated with the social sciences to successfully assess the behavior of violent offenders. At the leadingedge of the twenty-first century, how long will it take to actually, and consistently, reproduce valid results of the kind depicted in this movie as it concerns computer criminals?
To the already controversial debate that surrounds the investigative technique popularly known as profiling, fuel will here be added to the fire by posing two questions: (1) Can the behavior of computer criminals be dependably, reliably, and accurately assessed? (2) Can such an evaluation be undertaken remotely and successfully?Based on accounts spanning more than
55
30 years, wherein violent offenders have been successfully profiled, I believe the answer is “yes” on both counts. However, there are important distinctions between those whose crimes have, heretofore, been profiled— serial killers, rapists, and bombers — and serial computer criminals (crackers). Five are noted here.
First is the important issue of operationally defining one’s terms. The labelserial_offender has traditionally been applied to a criminal believed to have committed three or more of the same crimes (e.g., murder), in the same way (e.g., evidence of excessive brutality, referred to as_over-kill). Ted Bundy was convicted of murdering three women. But he is believed to have taken the lives of more than 25 other women in five states in a 4-year time frame (Douglas and Olshaker 1995). Gilbert Escobedo confessed to raping 48 women. Authorities believe he violently assaulted twice that many victims in the Dallas area between 1985 and 1990 (Hazelwood and Burgess1989). Theodore Kaczynski, the infamous Unabomber was responsible for the murder of 3 and serious injury of 23 others in his 17-year reign of terror (Graysmith 1997).
But it is not hyperbole to assert that in a single event, a lone computer criminal, or cracker, can victimize hundreds of thousands of individuals and thousands of systems worldwide in a matter of nanoseconds. How then shall the termserial_be applied to such an offender? Does one virus that infects thousands unleashed by an individual, such as the recent MyDoom Virus (Lemos 2004), warrant being labeled_serial? How do authorities know — if the cracker does not take credit — when a subsequent cyber attack is perpetrated, who is responsible? And even if someone does take credit, can we be certainthat the person contending they are responsible is actually to blame for either incident? These are not idle or irrelevant questions. They are substantive both from a pragmatic (criminal investigative), as well as an academic (research) perspective.
I will contend that for computer criminals, like most rapists, the act for which they are apprehended is rarely the first offense (Hazelwood and Burgess 2004). Of the original cohort of FBI agent profilers, Roy Hazelwood, now retired, is one of the most prolific authors and consistent contributors to the scholarly literature on the subject. He advises that his research is consistent with the findings of Hunter (2001), Abel and Rouleau (1990), et al. In these studies rapists admitted to having sexually assaultedan average of between 7 and 20 women before they were apprehended the first time (Hazelwood 2004). I will contend that there is a parallel of predation with crackers. They likely have perpetrated many more than the standard three criminal acts or unauthorized intrusions before they are caught the first time. The estimate — 7 to 10 offenses — is also probably excessively conservative with respect to crackers. Some (too many) cyber predators have yet to be apprehended for their illegal transgressions. What then are the consequences of adjudication?
With conventional violent offenders, the track record for rehabilitation is not stellar. I suspect the same will be the case with many crackers. But the cybercrime phenomenon is too recent and the data too sparse tobe able to make any credible assertions, let alone inferential statements about an unknown population, with regard to recidivism rates. Anecdotally, some who have been apprehended (black hats) have subsequently turned their skills to information security.Throughout the field such individuals are referred to asgray hats(Interpol 2002).
Second, violent serial offenders are always physically present at the crime scene. Computer criminals are almost never at the same location as their victims. The latter group routinely attacks victim systems far removed from their own physical location. Whereas a killer, rapist, or bomber is almost always vulnerable to detection during the commission of each crime, the computer criminal’s actions are almost never detected until well after the attack has occurred and the attacker is safely distant from the literal crime scene.
Third, reviewing a murder crime scene involves the examination of tangible elements such as fluids, hair, and fibers. Evidence of a computer crime requires the assessment of invisible electronic zeroes and ones. Such evidence must be extracted from firewall logs, Intrusion Detection System (IDS) alerts, file servers, and so forth. The basic methodology involves what some authorities have referred to ast__he three A’s: (1) acquiring the evidence without altering or damaging the original, (2) authenticating that the recovered evidence is the same as the originally seized data, and (3) analyzing the data without modifying it (Kruse and Heiser 2002, 3).
Fourth, the span of influence is different. Whereas the serial killer’s actions impact three or more victims (as well as their families, friends, and neighbors), the reach of the serial computer criminal may damage thousands of systems and endanger the lives ofliterally millions of people. For example, a cyber attack directed at a nuclear power plant could result in the release of radioactive material into the atmosphere that could cause the death or debilitation of countless victims.
Finally, the more adept thekiller, rapist, bomber, or computer criminal, the better able they are to cover their tracks, that is, destroy or delete evidence, physical or digital, from the crime scene. However, with physical crimes, it is nearly impossible to remove all evidence, particularly so-called trace or microscopic evidence that is invisible to the naked eye and therefore overlooked. But, in the case of computer crime, the greater the offender’s skill set, the greater is the likelihood that they will be able to irrevocably eliminate all traces of the attack from the system assaulted, and to do so in a matter of seconds. This last is one of the most ignominious aspects of computer crime investigations.
One other distinction is important to highlight before proceeding: The mediahas dubbed those who commit computer crime ashackers. This is unfortunate. The termhacker_has a venerable and reputable origin. In the 1960s, when computer memory was precious, it was desirable as well as seen as evidence of a high level of skill and egalitarianism to reduce the lines of source code to the absolute minimum while retaining the application’s full operability. The procedure, referred to as_hacking, was regarded as an indication of the competence of the programmer, called a hacker (Levy 1984). The discussion here focuses on individuals who will be referred to as crackers._Crackers_are here defined as those who repeatedly use their technical skills and knowledge in violation(s) of the law and/or whose unauthorized intrusion into systems damages those systems or the data therein.
Before building a case for the proposition that crackers can be profiled, I will endeavor to clarify and expand the foundation of this arcane discipline. The purpose is to expose the myths about profiling in order to enable the reader to consider what from this knowledge base may be applicable to the assessment of the unique mannerisms, quirks, and characteristics of serial computer criminals (crackers).
I.Annals of Profiling
The FBI popularized offender profiling in the mid-1970s. Since the early 1990s, the FBI has referred to what they do as criminal investigative analysis. But the old phraseology endures; for the popular press and law enforcement itself, even within the FBI,the term_profiling_continues to be used. Applied to serial computer crime investigation, a more apt descriptor, even if not as pithy, is proposed: cyber investigative behavioral assessment (CIBA). This phrase will be operationally defined. Described heretoo will be the history: premodern, its heyday — the FBI era — as well as contemporary times, of profiling. Various definitions will be presented. CIBA will then be operationally defined, and the rationale for doing so will be suggested. The literature onthe topic will, of course, be reviewed. The discussion will include various mitigating, often conflicting, factors surrounding the use of profiling. Philosophical considerations, investigative and administrative issues, as well as related and scholarly concerns will be reviewed.
The primary use of profiling continues to be applied to the kinds of crimes for which it was honed: murder, rape, and, comparatively speaking, the less frequently occurring bombing and other terrorist acts (Hudson 1999). Although there is a nexus between such crimes and human sexuality, as well as behavioral and mental disorders, these topics will not be addressed.
There simply is insufficient data available to venture down this uncharted path. The phases of serial murder and rape will be outlined to determine what if any parallels exist with computer crimes. Offender typologies, victimology, and the behavioral assessment of the crime scene for both of these specific crimes will be alluded to, again, to consider what similarities might exist in the case of serial computer crimes. Finally, the expectation for the future of profiling generally and computer crime profiling specifically will conclude this discussion.
II.History
The individuals who have contributed to the annals of profiling are colorful in their own right. But there is insufficient canvas here to paint a portrait of any of them. Instead a few brushstrokes will be applied to help put into perspective a sketch of a topic that both fascinates and frustrates policing practitioners, the public, andpundits alike. By and large, the popularity of profiling can be laid at the doorstep of the FBI facilitated in large measure by the media’s fascination with the technique. There are precursors and contemporary adherents whose contributions will be brieflynoted as well.
A.Premodern Antecedents
The first documented use of psychological profiling dates to the mid-1940s. Toward the end of World War II, psychiatrist Walter C. Langer and three of his colleagues were tasked with an unusual and groundbreaking assignment. The Office of Strategic Services (OSS), precursor to the Central Intelligence Agency (CIA), asked them to scrutinize the behavior of Nazi Germany’s fuehrer, Adolf Hitler. By studying his every move, the OSS hoped Hitler’s actions could be predicted. The report, which numbers more than 250 pages, concludes with a section entitled “Hitler’s Probable Behavior in the Future” (Langer 1943).
To their credit and remarkable acumen, these physicians assigned probabilities and likely consequences for each possibility they outlined. Eight contingencies were set forth in their report: The military might revolt and seize Hitler, or he may seek refuge in a neutral country, fall into allied hands, get killed in battle, die of natural causes, go insane, be assassinated, or commit suicide. Two of these prospects are striking: assassination and suicide. The former was in fact attempted. On July 20, 1944, Lieutenant Colonel Count Klaus von Stauffenberg is credited with orchestrating the failed effort to end Hitler’s life with a bomb at his East Prussia headquarters. The latter appraisal is even more remarkably prophetic (Langer 1943, 247–248):
This is the most plausible outcome…. being an hysteric he could undoubtedly screw himself up into the super-man character and perform the deed. In all probability, however, it would not be a simple suicide. He has too much of the dramatic for that and since immortality is one of his dominant motives we can imagine that he would stage the most dramatic and effective death scene he could possibly think of…. He might even engage some other fanatic to do the final killing at his orders.
On April 30, 1945, in his Reich Chancellery bunker in Berlin, Hitler and Eva Braun, his bride of 1 day, indeed took their own lives. Thereafter, someoneremoved the bodies from the bunker and set them ablaze. Who did so remains a mystery to this day. Although the precise date of the report is unclear, it seems reasonable to infer that it was issued well before the assassination attempt and clearly prior to the suicide. In an interesting coincidence, the charred bones of German cracker Karl Koch (Hagbard) were located in an isolated forest following the indictment of him and his associates: Hans Huebner (Pengo), Peter Carl, Dirk Bresinsky, and Markus Hess.This discovery followed the March 2, 1989, indictment by German authorities of the so-called Hannover Hackers for espionage. If Koch left one, the police did not find his suicide note (Stoll 1989).
The next verifiable use of profiling — the first in a criminal investigation — occurred in the mid-1950s. In this instance it was a grasping at straws that subsequently appeared to have been a stroke of genius. Beginning in 1940, over a period of more than a decade, 54 devices were placed in New York City, 37 ofwhich exploded. These resulted in the maiming of 22 people. Amazingly, no one was killed in the perplexing bombings of public facilities. The first was detected November 16, 1940, a pipe bomb that had been placed on a West Sixty-fourth Street windowsill. This device was discovered, dismantled, and rendered harmless. Over the next 10 years several more bombs exploded at major New York City landmarks: Penn Station, Radio City Music Hall, the Empire State Building, Macy’s Department Store, the Fifth Avenue Public Library, Grand Central Station, and others. Even when bombs failed to explode, however, the effect of their being detected nevertheless exacerbated public consternation.
Dubbed “The Mad Bomber” by the media, it was clear that the person responsible forthe bombings held a grudge against Consolidated Edison (Con Ed) the city’s power company, where the first device was discovered. This became evident because of the content of the letters sent to various newspapers in which Con Ed was castigated. The letters were always signed “F. P.” When arrested the bomber said the initials stood for fair play — something sought, but not received from Con Ed. Through the mid-1950s, traditional investigation had turned up little in the case. But no one had been seriouslyinjured nor complained loudly enough to generate more than perfunctory activity from the New York City Police Department (NYPD). Following the December 2, 1956, bombing of Brooklyn’s Paramount Theater, however, six people were injured, three of them critically. Police Commissioner Stephen Kennedy felt compelled to make a public statement. A reassuring press release was issued. NYPD’s crime lab director, Inspector Howard Finney, knew the commissioner’s verbal balm would not soothe. Something more had to be done. In a second press release he announced that psychiatrist James A. Brussel had been retained to study the behavioral aspects of the Mad Bomber case.
The behavioral portrait Brussel constructed turned out to be amazingly accurate. After painstakingly reviewing all of the available data, Brussel concluded that the Mad Bomber was paranoid, fixated, obsessively meticulous, narcissistic, and sanctimonious. He worked for or had been employed by Con Ed. He was someone who saw himself both as victim and avenging angel. The detectives listened passively to this part of the assessment. They had already figured this much out by themselves. Finney then asked for a description. The psychiatrist hesitated but complied. Brussel said the bomber was symmetrically built.This raised the eyebrows, as well as the skepticism, of these conventionally minded and trained investigators. Even when explained point-by-point, the remainder of the profile seemed even more incomprehensible.
Brussel said that the bomber’s ethnic originwas Eastern European, probably Slavic, and he was likely a Roman Catholic. English was not his first language. He had hidden Oedipal tendencies, no close friendships with men nor consequential relationships with a woman. Unmarried, he was probably still avirgin. He lived in Connecticut with a female relative, a spinster aunt or sister. He had or believed he suffered from a chronic ailment (heart disease, cancer, or tuberculosis) and that Con Ed was responsible for his malady. He was a polite, cooperative,fastidious, clean-shaven, middle-aged white male, neatly dressed. When located, he would be wearing a double-breasted suit, buttoned. This last was almost too much for the incredulous detectives to accept.
To their credit, the police did not dismiss the unbelievable assessment. Armed with Brussel’s profile and under the command of Chief Inspector Edward Byrnes, the newly established Bomb Investigation Unit set about to track down the Mad Bomber. Comparing Workmen’s Compensation Board claims with former employee personnel records, the file of a United Electric and Power (Con Ed’s precursor) generator wiper was located. This person had filed a claim for permanent disability pay. He believed that he had contracted tuberculosis as the result of an on-the-job accident in which a backdraft of hot gases from a boiler had knocked him down. The company denied the claim. A 3-year letter campaign of complaints followed thereafter. The last entry in the file was dated 1937. Subsequently, nothing more was heard from the claimant. The first bomb was placed 3 years later. This information was discovered late Friday night, January 18, 1957.
The following Monday morning, January 21, 1957, detectives drove to the last known address of this person. To the amazement of the arresting officers, every point of Brussel’s assessment was accurate. When he was taken into custody at the Waterbury, Connecticut, home of his two unmarried sisters where he lived, 53-year-old George Matesky was wearing a doublebreasted suit, buttoned (Douglas and Olshaker 1996).
Part of Brussel’s assessment (fixated, obsessive, meticulous, narcissistic, and sanctimonious), isvery interesting. A significant number of accounts of interviews with and field observations of suspected crackers manifest these same characteristics. Although there is insufficient data to generalize to the entire population of serial computer criminals,it is reasonable to assume that these traits are parsimonious.
There are some striking and very interesting parallels between Matesky and a more recent infamous bomber, Theodore Kaczynski. Dubbed “The Unabomber” by the FBI, Kaczynski’s 17-year odyssey hasbeen chronicled in several books, including the very well balancedUnabomber: A Desire to Kill(Graysmith 1997). The Unabomber too was accurately profiled in 1993, but that assessment was not acted upon (Witkin 1997). Other events brought Theodore Kaczynski to justice (Scripps-Howard 1996).
B.The FBI Era
In the late 1960s, FBI Supervisory Special Agent (SSA) Howard Teten began corresponding and consulting with Brussel about the concept of behavioral assessment. Teten and his partner, SSA Pat Mullany, wereteaching applied criminal psychology at the FBI Academy. SSAs Richard Ault, Robert Ressler, and others became interested as well in this arcane subject and were mentored by Teeten and Mullany. Teeten began talking about the Mad Bomber case specifically, and profiling in general, in their National Academy (NA) classes. Many of their police officer students were intrigued. Upon returning to their agencies following their NA training, some began calling back to Quantico to ask for advice on open, unsolved murder cases.
In the mid-1970s, SSAs Ressler and John Douglas began conducting interviews of incarcerated known serial killers. This they accomplished on their own time while assigned to conduct so-called road schools, 3- to 5-day training that had been requested by law enforcement agencies. The interviews were conducted in prisons near these training sites.
The real breakthrough in the development of a knowledge base occurred, however, between 1979 and 1983. With input from the entire membership of the Behavioral Science Unit, a sophisticated protocol (interview questionnaire) was developed. Thereafter, this instrument was utilized to collect data for input into a not-yet-operational, specially designed, computerized analytical program. With the new protocol,data from 36 convicted sexual killer interviews were utilized. Actually, more than 36 interviews were conducted, but because of blatant obfuscation and verifiable fabrication, only 36 were included in the analysis.
In addition, data was compiled on 118 victims, most of whom were women. At this juncture, SSA Roy Hazelwood joined Douglas and Ressler. He took part in the majority of these latter interviews. A great deal was learned from and about the killers themselves. This data was independently corroboratedwith investigative and forensic documentation (Egger 1990; Jackson and Bekerian 1997). In this same time frame, police officers from around the nation increased requests for assistance from the Behavioral Science Unit, whose other faculty members by now were conversant with Teten’s pioneering initiative.
In March 1984 the FBI received a $3.3 million grant from the National Institute of Justice (NIJ). The purpose of this grant was to fund the organizational development of the National Center for the Analysis of Violent Crime (NCAVC) and to implement the computer-aided Violent Criminal Apprehension Program (VICAP). The NCAVC was established at the FBI Academy, Quantico, Virginia, and became operational in May 1985; the Behavioral Science Unit was then mergedwith the NCAVC.
VICAP was the brain-child of the late Pierce Brooks. Retired from the Los Angeles Police Department, he was a renowned homicide detective and subsequently served as chief of police of Eugene, Oregon, and Lakewood, Colorado. Brooks had longbelieved in the sharing of resources and information, as well as consultation on complex investigations. Doing so, he reasoned, would add substantially to the solution of unsolved serial murder and rape cases, as well as missing person cases. As an NIJ consultant to the FBI on the 1984 grant, Brooks envisioned VICAP as the means to that end and the NCAVC as the national clearinghouse for such knowledge.
Initially, reports of solved and unsolved murders and rapes were entered into the VICAP database. Later,other crimes were added. It was expected that detectives from throughout the nation would eagerly complete VICAP reports and routinely submit them to the NCAVC. Data mirroring the volume of homicide and rape cases nationwide was anticipated to routinely, steadily, and immediately flow into VICAP. Each time a new unsolved case was received, the data was input and the elements compared with like factors previously entered in the database. If there were similarities that matched between characteristics of thenew case and one (or more) already entered in the database, the system would register the correlations. When this happened, notice was sent to the respective law enforcement agencies. This would enable the agencies’ detectives to compare notes and bring the cases to successful conclusions.
In principle the concept was elegant, the intent noble. But VICAP never achieved its potential. In large part this was due to factors beyond the control of the FBI. Simply and bluntly stated, it was a matter of indolence.Police detectives complained that the VICAP form was too long and took too much time to complete. Recognizing the necessity for cooperation in these voluntary submissions, the form was revised and streamlined down to 15 pages (189 items). But still the complaints continued; the submissions became a trickle not a torrent. Without a steady flow of data — the lifeblood of any system — the chances of successfully matching unsolved serial crimes diminished.
The heyday of the NCAVC was probably from 1985 to 1995. In that decade a number of significant undertakings were achieved. For example, several Behavioral Science Unit members authored a large number of journal articles and a handful of books on profiling and serial murder, rape, and arson. These publicationsadded considerably to the previously meager body of knowledge in this domain. VICAP and its parent, NCAVC, serve, it seems, as perfect models as infrastructures to support the basis for profiling of computer criminals (Reboussin 1990).
Another innovationwas an artificial intelligence (AI) computer program developed under the direction of a Ph.D. Electrical Engineer David J. Icove. In 1990, he and two other members of the Behavioral Science Unit completed a 5-year project to bring online a LISP-based Expert System built on a then state-of-the-art platform, a DEC VAX 11/785 minicomputer. The intent of this project was to have the system serve as an automated assistant for human profilers (Reboussin 1990). The system, dubbed “Profiler,” never made it beyond prototype stage. This project too has been subsequently discontinued. But again it would appear to be a perfect vehicle for capturing the knowledge base of the unique mannerisms, quirks, and characteristics of computer criminals.
Perhaps the most visionaryin this sequence of FBI accomplishments, however, was another since-cancelled undertaking. Roy Hazelwood oversaw the 10-month Police Fellows program that also began in 1985. The curriculum was designed to train seasoned homicide investigators in the skillsof profiling. By January 1990 two dozen police profilers had been trained. In this group of 25 were investigators from 12 different police agencies, and eight detectives from major metropolitan agencies. Also trained were two secret service agents and twoagents of the Bureau of Alcohol, Tobacco, and Firearms. In addition, one member of the Royal Canadian Mounted Police was so trained. Training a geographically diverse cadre of specialists that could provide assistance to agencies in surrounding jurisdictions in those cases that appeared to be the work of a serial offender was the FBI’s goal.
FBI agents in the field also received training, but their training was of a shorter duration and for a different purpose. Once trained, these field agents, designatedprofile coordinators, were to serve as liaisons between local law enforcement agencies and the Behavioral Science Unit at the FBI Academy in matters that related to the investigation of serial crimes. Of the many reasons for regretting the cancellation ofthis particular program, at the top of my list is that the NCAVC would have provided the perfect infrastructure for training a cadre of computer crime profilers. Although many may now contend that no one could have predicted the deluge of computer crime weface today, there were at the time some whose Cassandra-like forecasts fell on deaf ears. The NCAVC has also undergone organizational changes, and VICAP has been operationally modified.
C.Successes and Failures
Comparable commentary cannot be offered with regard to the success or failures of profiling. That is so due to the confidential nature of the use of profiling. Its use does not lend itself to chronicling the events, places, and people involved until after the case is closed, if at all. That is, only until and unless someone has been charged with the crime(s) is such information made available for public consumption. If charges cannot be brought against the offender(s), it is unlikely that investigative techniques — such as profiling — will be revealed. The exceptions are few and far between. Some have been featured in the print and electronic media, usually to the consternation of the profilers, the chagrin of the law enforcement agency with jurisdiction, and the choleric indignation of the prosecutor.
A review of the literature on profiling in a later section will make note of the contributions that have been made recently in this field by practitioners, former practitioners, scholars, researchers, and journalists. Dramatists have contributed as well. Some have published lifelike fiction as well as recounted the escapades of certain true-life serial killers. The accounts of some serial computer criminals have also been chronicled by the Fourth Estate in recent years, most notably the notorious Kevin Mitnick (Shimomura and Markoff 1996).
III.Profiling Defined
A great deal of confusion still remains about profiling, despite the fact that the termprofiling_is readily recognizable and in wide public use. One reason has to do with the lack of a uniformly agreed upon definition. Plato (c427–347) said that if one is preparing to engage in a discussion of 4 hours duration, 2 of the 4 hours should first be spent defining one’s terms. This important admonition has too often been overlooked to the detriment of many discussions, and specifically as it concerns the topic of profiling generally as well as computer crime profiling specifically. Another reason for the confusion has to do with the media attention (print and electronic) that has focused on profiling. Responsible television journalism, such as Bill Curtis’s A&E_Justice Files, PBS’sNova, and similar History Channel programming, have reported on the use of criminal profiling. Unfortunately, there are also wildly exaggerated fictional depictions of profiling. These, unfortunately, receive a larger share of the public audience than do the programs that are true to life. The current crop of exaggerated fictional shows includes the aptly titledProfiler_and_Millennium, both NBC television weekly shows. And thereis, of course, Fox television’s runaway sensation now in syndication,The X-Files.
There is no generally accepted definition of offender profiling. What it is and what is its purpose is widely debated. A number of terms have been used to characterize the same thing. In addition to the succinctprofiling, the following appellations are also used synonymously: criminal profiling, offender profiling, criminal personality profiling, psychological profiling, profile analysis, and the FBI’s criminal investigative analysis.
One definition depicts profiling as “a means of examining through forensics and the behavioral sciences possibilities derived from an incident that has already occurred.” This author further states that “the best that can be hoped for is to better understand the crime, its perpetrator, and his motivation” (Kelleher 1997, 14).Another definition states that the purpose of profiling is “to identify and interpret certain items of evidence at the crime scene which would be indicative of the personality type of the individual or individuals committing the crime” (Swanson, Chamelin,and Territo 1984, 700–701). The FBI’s Hazelwood and Douglas (1980, 5) defined profiling as the following:
An educated attempt to provide … specific information as to the type of individual who committed a certain crime…. A profile is based on characteristic patterns or factors of uniqueness that distinguishes certain individuals from the general population.
Five years later, the FBI further refined this definition as “the process of identifying the gross psychological characteristics of an individual basedupon an analysis of crimes … committed and providing a general description of the person, utilizing those traits” (Ressler, et al. 1985, 3). The distinguishedDiagnostic and Statistical Manual of Mental Disorders(DSM-IV) does not include a definition of profiling (APA 1998).
A.CIBA Defined
Applied to the investigative niche of computer crime, a new, succinct definition for CIBA is offered that includes five criteria. First, it is aprocess, a procedure brought to bear in the evaluation of a crime scene. Second, it makes use offorensic evaluation(preservation, identification, extraction, documentation, interpretation, and statistical analysis of computer data). Third, it draws on the knowledge of certainsocial sciences(criminology, criminal justice, andsociology). Fourth, it draws upon a body of_clinical_knowledge from the medical and mental health professions (psychology, psychogenics, and psychiatry). Fifth, its purpose is to_narrow the focus_on the behavioral type or characteristics of an offender ina particular criminal investigation — computer crime. I have chosen to label this set of proposed criteria as CIBA. These propositions appear to be consistent and parsimonious with Kilger’s MEECES conceptualization (Kilger 2003). Such compatibility will go a long way to further the scientific rigor of CIBA.
CIBA more aptly describes what is involved in the profiling of computer criminals. Several additional considerations are offered. First, the domain of its use, at least since the 1980s, has been and continues to be primarily criminal investigations. Second, use of the wordpsychological_is rejected. The assessment rendered is not based on an interview of the subjects (suspects) themselves. The disciplines of psychiatry and psychology are steeped in the tradition of one-on-one interviews and consultation. The clinician’s work with a patient often involves several sessions before a diagnosis is rendered. That is never the case in the use of the procedures under discussion. Thus, the qualification in the definition offered: the clinical_knowledge, rather than their skills. Third,_psychological_is rejected on another count: The word excludes consideration of other factors or quirks that the digital crime scene may reveal. For example, file-naming conventions are frequently matters of convenience rather than specific, necessary technical necessities. But the use of certain phraseology may suggest a behaviorally relevant idiosyncrasy that may not be a simple anomaly but rather a telling marker.
IV.Review of theLiterature
The foundation in the profiling niche was clearly laid by the FBI. Articles and books have been authored by several members of the FBI Academy’s Behavioral Science Unit (e.g., Ault and Reese 1980; Hazelwood and Douglas 1980; Hazelwood 1983; Ressler 1985; Lanning 1986; Icove 1986). Others are the writings of non-agent FBI personnel (e.g., Pinnizzotto 1984; Howlett et al. 1986; Reboussin 1990). Some are FBI agent collaborations with scholars (e.g., Ressler and Burgess 1985; Douglas, Ressler, and Burgess 1986;Douglas et al. 1986, 1992; Ressler et al. 1986; Hazelwood and Burgess 1987, 1989; Ressler et al. 1988; Hazelwood and Warren 1989, 1990; Dietz et al. 1990). Since retiring from the FBI, some of the Behavioral Science Unit personnel have contributed additional material to this body of knowledge (e.g., Douglas and Olshaker 1995, 1996, 1997, 1998; Ressler and Shachtman 1994, 1998; Vorpagel 1998; Icove et al. 1998; Hazelwood 2004).
Other law enforcement officers have also made important contributions (e.g., Keppel 1989, 2003; Geberth 1981, 1990; Kelsoe 1996). From outside the United States important contributions to the literature include thoughtful works (e.g., Copson 1995; Rossmo 1996; Canter and Alison 1997; Jackson and Bekerian 1997; Marshall et al. 1998). Journalists too have contributed to the literature in important ways, both in fictional accounts (e.g., Bruno 1995; Carr 1994, 1997) and nonfiction (e.g., Graysmith 1997; Bruno 1993; Cahill 1987).
Physicians and academicians have contributed to this genre (e.g., Samenow 1984; Egger 1984, 1998; Dietz P. E. et al. 1990; Hickey 1991; Turco 1998). Criminologist Eric Hickey has carefully articulated the present-day picture of profiling in the United States. Synopsizing novels and nonfictional tract, text, and treatise, he draws a comprehensive picture of modern profiling (Hickey 1991).
An excellent perspective of the European experience is provided by Dutch and British scholars, respectively, Jackson and Bekerian (1997). The contributors in this anthology succinctly describe the research that has been conducted in the past 15 years. Sociologist Lundgren (1997) critically examines the prevailing social/psychological model. He makes a case for the way in which this model has become dominant in serial murder cases. Experimental psychologists Zagrodzka and Fonberg, in Feshback and Zagordzka (1998), ask whether predatory behavior is a model of complex forms of human aggression. Myers and Burgess, in Van Hasselt and Harsen (1998), discuss the major theoretical perspectives of serial murder and sexual homicide. Psychiatrist Ross (1998) makes a compelling case for reassessing the way in which violent criminals are dealt with by society.
As it relates specifically to computer crime investigation publications, little about profiling has yet to appear with any consistency in this segment of the literature. Notable exceptions in texts include the work of Kilger et al. (2002), Gudaitis (2001), and Casey (1999, 2000). Standout journal articles include the contributions of Edmond and West (2003), Gudaitis (2000), and Greenfield (1999).
V.Uncertainties
A number of problems must be dealt with in any criminal inquiry. This is generally so in a homicide investigation and especially in a known serial killer investigation. Four areas will be addressed here that relate to computer criminal profiling: conceptual considerations, investigative dilemmas, interagency obstacles, scholarly concerns, and related issues.
A.Conceptual Considerations
Philosophically there are some important considerations associated with profiling. There are legitimate authorities, and there are charlatans who claim expertise as profilers. There are three categories of American investigators I regard as authentic profilers. FBI agents (active duty and retired) who have trained at the FBI Academy’s Behavioral Science Unit are one category. (Of course, not all FBI agents receive this training.) Other law enforcement officers (active duty and retired) trained by the FBI, are also qualified profilers. The third group constitutes the handful of criminal investigators (active duty and retired) who were trained other than at the FBI Academy but who, nevertheless, are legitimate profilers. In my estimation, there are fewer qualified profilers in this latter category.
Outsideof law enforcement there are also individuals qualified to construct a criminal profile — some physicians, for example. Psychiatrists specifically educated in dealing with abnormal human behavior and experienced at interviewing criminals could do so, as did James Brussel in the Mad Bomber investigation. Under the best of circumstances, however, it is difficult to assess human behavior. Some of the most talented of such psychiatrists have been duped by savvy criminals (Samenow 1984; Yochelson and Samenow 1976). Scholarly individuals with graduate degrees in a social science discipline such as psychology fall into a gray area. This is because it is a rare academic who has had hands-on experience. Few have interviewed a known or acknowledged serial offender. Fewer still have examined a crime scene. Reading about profiling does not make an expert profiler, and talking to a self-described hacker or cracker does not make an expert cyber profiler.
Lacking an appropriate background but having a gift for gab and familiarity with the jargon, empirics take advantage of the gullible and desperate. Amongst the unscrupulous are those who have no relevant education, training, nor experience. Unfortunately, some of these opportunists are former law enforcement officers; stillothers are lettered. As in any endeavor in life, the watchword for the prospective employer iscaveat emptor(buyer beware). A useful rule of thumb is to check the bona fides of the prospective consultant (profiler). If they are legitimate, they will havean established reputation and a verifiable track record. NDAs (nondisclosure agreements) notwithstanding, profilers who offer their services should be willing to identify the law enforcement agencies and/or corporations where they have undertaken profiling consultations and their points of contact.
B.Investigative Dilemmas
A major hurdle not easy to overcome is that the senior detectives, who typically investigate homicide or computer crime cases, frequently lack a background in the behavioral sciences. They may also dismiss outright the utility of the behavioral sciences generally and profiling specifically. Their examination of a crime scene may thus overlook important behaviorally relevant clues. Another problem is that the first responder may be an inexperienced patrol officer who also lacks relevant training. This lack of experience may result in the crime scene being compromised. As it concerns computer crime scenes, disturbing the crime scene may mean destroying the evidence. A third problem is thatthere seems to be a direct correlation between the spectacular nature of the crime and the number of unassigned personnel who show up at the crime scene. It has not happened yet in a computer crime case — but it will. Unless organizationally prohibited, some who have no need to be at the crime scene will nevertheless make an appearance. They want to look around and will sometimes push their way past the rookie protecting the crime scene. Executives, who ought to know better, are sometimes the worst offenders.
C.Interagency Obstacles
It is not uncommon for serial offenders to commit their crimes in more than one jurisdiction. But agencies conduct investigations as they present themselves sequentially, usually singly. By the time a series of serial cases becomes evident, multiagency involvement frequently becomes obvious and inevitable. Each agency finds itself in a situation in which it must interact with one or more other agencies. Inevitably, each believes they should be in charge. Predictably, each believes their way of doing thingsis superior to the way the other(s) are handling the investigation. Insecurity turns to defensiveness that leads to obstructionism. Failure to share, cooperate, or coordinate information are the major ways in which displeasure is expressed over the undesirable situation.
This confounding circumstance is what Egger (1984) termed “Linkage Blindness,” which is the unwillingness of the agency head (or some other authority figure) to admit that outside assistance is needed to solve a case in their jurisdiction.As it concerns computer crimes, bringing in a consultant does not yet seem to have been a widespread problem — but it will. Linkage blindness is most evident when agencies at different levels must interact. For example, when a suburban agency must work with a big city agency, when a municipal agency must work with a state agency, or when any of the former must work with a federal agency. This can occur intra-agency as well. The desire for glory, promotion, or even something as trivial as overtime pay has driven some detectives in one unit to hold back information from investigators in another unit within the same agency. This problem has surfaced in several high-profile serial murder investigations: David Berkowitz, Larry Eyler, and Ted Bundy, to name but three (Douglas and Olshaker 1998). This amounts to cutting off one’s nose to spite one’s face. But it happens consistently. I postulate that this is not solely an American phenomenon. Petty professional jealousy and insecurity has long existed in law enforcement. There is little indication that the problem will soon resolve itself or that computer crimes will be exempt.
D.Scholarly Concerns
The FBI’s profiling program too has its detractors. One highly qualified critic asserts that it “lacks … validity and reliability … and … a proper theoretical basis” (Rossmo 1996, 71–72). Another skeptic contends that the inferences drawn from the data rest on too meager a baseline. That is, the original sample size was inadequate (Copson 1995). There are also those who question the utility of profiling altogether (Levin and Fox 1985). In spite of such controversy, to a large extent “many, if not all, of the psychological profiling units in other countries have been modeled on the FBI approach” (Jackson and Bekerian 1997, 6). It is also noted that renowned psychiatrist and adviser to the American Psychiatric Association Park Elliott Dietz applauds the work of the FBI. He says, “I think I know as much about criminal behavior as any mental-health professional and I don’t knowas much as the Bureau’s profilers do” (Michaud 1986, 42). Although expertise in this investigative niche may not be easy to objectively evaluate, its mantle continues to be bestowed upon the FBI. For this reason, if no other, it is hoped that the FBI willbe the vanguard for the development of the first wave of certified cybercrime profilers.
E.Related Issues
Professional recognition of profiling as a legitimate technique, at least in the United States, lacks academic standing. Few institutions — I know ofnone — confer a degree in this esoteric field. Just over two dozen institutions have recently been identified that do offer coursework in this domain. Some schools in the United States that have been noted for the quality of their programs are the Illinois School of Professional Psychology, Fielding Institute (Santa Barbara, California), University of Virginia, and Northwestern University. The only cyber counterpart that has surfaced, thus far, is the CyberPsychology Institute at Brandeis University (Waxman 2003).
There is also a lack of published work or organizational reporting. Too little of it reports scholarly research with a sufficiently large baseline to be able to infer from a sample to its population of offenders or to assess the accuracy of the techniques utilized. Fortunately, an excellent source of material concerning conventional profiling is available at the FBI Academy Library, thanks largely to the efforts of Ms. Cynthia Lent. Quantico probably holds the single largest collection of profilingliterature in the world. It is expected that the FBI Academy will also become the major repository for computer crime profiling literature. “Profiling,” a chapter in the forthcoming second edition of_Know Your Enemy_by the Project Honeynet staff (Kilger,Arkin, and Stutzman 2002), will make a significant contribution to this embryonic niche of the profiling literature. Insofar as violent crime profiling practitioners are concerned, the most reputable and experienced of the consulting firms in this arcane domain is the Academy Group of Manassas, Virginia. Many of the profiling pioneers, the original FBI Academy Behavioral Science Unit faculty, constitute its primary staff. A cyber counterpart of such expertise has not yet emerged publicly.
VI.Education andTraining
In the past, training, investigative consultation, and research were available almost exclusively from the FBI. This limitation virtually ensured that the majority of law enforcement investigators would never receive training in this esoteric topic. Increasing interest by individual scholars and researchers has changed this situation. Still, criminal justice and criminology curricula should be further expanded in this regard. So should the offerings in psychology and sociology departments. Most university and college courses in these domains that offer anything beyond a course or two in abnormal behavior are practically nonexistent. A notable recent exception is the School of Public Safety and Professional Studies at the University of New Haven, where one may earn a master’s degree in criminal justice with a forensicpsychology concentration (Monahan 2003).
Some additional suggestions are offered that will enhance law enforcement’s ability to identify the behavior of serial violent offenders, as well as computer criminals. For example, many law enforcement agencies today hire candidates who hold a bachelor’s degree. At the federal level, a baccalaureate has long been an explicit entry-level requirement. For state, county, and municipal law enforcement, a college degree is today a de facto condition of employment in a high percentage of such agencies. At least annually, detectives assigned to investigate serial violent offenses and computer crimes should receive a minimum of 40 hours of instruction in advanced behavioral sciences.
The case study method could also easily be incorporated into such training. This undertaking simply requires that law enforcement chief executives authorize their directors of training to assign a staff member to orchestrate the instruction. Blocks of instruction in the behavioral sciences for all police officer basic training academies should be increased. In most law enforcement agencies the least amount of time is devoted to behavioral sciences as compared to any other topic in basic academy curricula. Heightening the awareness of recruits is important because it is often the least seasoned officers who are assigned to secure a crime scene of a violent crime or cybercrime. Knowledge of serial offender patterns would enable these officers to better protectthe crime scene until the arrival of crime scene analysts and detectives. For criminal justice and criminology majors, a practicum or internship should be required. Virtually every police officer that, as a student, had such an experience has raved aboutthe value of this experience. A number of academic institutions recognize the importance of such an experience for their students and align themselves with the law enforcement community to facilitate a more encompassing educational experience that will enable and enhance the process of profiling.
VII. Science or Art?
Some dismiss art as less important an exposition of reality than science. The elements of an oil painting are not quantifiable as in the case of chemistry, for example. There is great beautyin art. Sometimes without uttering a syllable, art can communicate excellence and precision, as in the familiar phrase, a picture is worth a thousand words. The artist is uniquely talented and, in their field, has capabilities far beyond those of most people, including the average scientist. Time is taken to address this distinction because of the kind of criticisms that have been leveled at profiling. Profiling has elements of both art and science. That it is not exclusively one or the other does not negate its utility. Nor is profiling any less valuable an investigative tool to aid in the type of criminal investigation for which it is intended than, say, blood typing is in determining that the dark viscous substance found at the crime scene is O-negative blood — probably human. Critical evaluation is an important feature of the scientific method. But denigrating profiling because it does not fit the status quo is adherence to dogma, not science.
A.The Status Quo
Conventional wisdom is critical of that which does not fit the well-established order of experience. It questions the validity and utility of whatever is not a traditional precept or maxim of the tried and true. The topic of resistance to change, particularly in policing, is well-documented. Like all disciplines, law enforcement has conventions that are long-standing and seldom questioned. This has been the case in criminal investigations, especially amongst homicide detectives. Here too there are accepted practices and procedures (rituals and incantations) that are passed on by the seasoned detective (wise old shaman) to the newly promoted detective (acolyte) who learns primarily through on-the-job training. The novice is told that, if they are to succeed, they must do what they are told by their elder without question. And the pattern repeats itself generation after generation. This pattern has been described as a model or paradigm.
Much has been accomplished by the established order, the discipline’s paradigm. However, from time to time the sacred tenets of the past fail to produce the expected outcome. Occasionally, those not tied to the old established order venture into new realms in search of ways to achieve desirable results. Those who do so, however, risk incurring the wrath of the defenders ofthe status quo. Thomas S. Kuhn (1996) set forth a grand theory of “paradigm shifts” in his 1962 landmark work,The Structure of Scientific Revolutions. This concept may already be applicable to profiling of serial violent criminal offenders. It could easily be the case for computer crime investigations if procedures are not established to thwart this malady.
B.Profiling Process
Profiling is intended to assist the investigator by directing attention — narrowing the focus — on specific behavioral traits discovered at the crime scene that are indicative of a series of serial crimes. The procedure is premised on the conviction that certain types of offenses reflect the personality type of the offender(s). These predators exhibit quite unique patterns of behavior. The tangible evidence and intangible pointers help to evolve the offender’s personality type. Indicators of the expression of rage, hatred, fear, and other emotions are difficult for the untrained to identify. The techniques used to help identify thesecharacteristics were developed in the mid-1970s to 1980s at the FBI National Center for the Analysis of Violent Crime. The ability to recognize these traits is most helpful in highly atypical and bizarre sexually oriented crimes. These types of cases lacka typical motive or suspect. In serial cases, conventionally trained investigators frequently overlook important behavioral clues because what they see doesn’t make sense and so is dismissed from further consideration. The more violent and abnormal the crime, the more beneficial profiling can be (Ault and Reese 1980).
Sufficient data has not yet demonstrated a parallel for serial computer criminals. Such findings may not be far in coming, however, because a longterm project is ongoing at the FBI Academy (Jarvis 2003). Profiling is not meant to substitute for a well-structured criminal investigation in a violent crime nor a computer crime.
A violent crime profile includes three basic components:
Crime commission reconstruction
Behavior exhibited during the attack
Post-offense behavior
A violent crime profile may suggest the following information about the offender:
Race, sex, and age range
Marital status
Sexual maturity level
Interpersonal communication development
General employment
Mode of transportation
Police record or lack thereof
Reaction to questioning by police
Probability of having committed similar offenses
Likelihood of striking again
These factors are also relevant in computer crime profiling. The entire basis for anaccurate profile relies on the exceptional examination of the crime scene, whether it be in the physical world or the digital realm. Also essential are detailed interviews of victims and witnesses. Cursory interviews can result in critical delays in acquiring crucial information or in losing that information altogether. Important elements of the predator’s behavior and/or personality type can be surmised and assessed in hopes of properly directing the investigation. Several things may suggest themselves:
Discernable pattern
Linkages to other like crimes
Suspect pool generated and prioritized
Investigative direction
Motive
Containment strategy
Proactive techniques
Interview and interrogation tactics
Although I will contend that a profiler should be a behavioral scientist, detectives and police officers can and should be trained to recognize behavioral characteristics at the crime scene. The evidence may be indicative of the offender’s emotions and personality traits (Ault and Reese 1980). Generally, police officers will be the first responders at a crime scene, including, perhaps, computer crime scenes. First responders can either protect and preserve the crime scene or inadvertently destroy valuable behavioral — as well as physical and digital — clues left at the crime scene.
C.Risk Levels
Individuals and their home computers are certainly vulnerable to attack or victimization by many means, such as from stalkers, pedophiles, pornographers, identify theft crackers, and other cyber predators. A host of personal dynamics contributes or leads to vulnerability. Still, the risk levels described here will focus on systems’ dynamics rather than individual activity per se. Certain dynamics related to the victim system bear great impact on the investigation and the ability of the detective to solve that crime. For example, when employees leave an organization, are their user names and passwords immediately revoked or is there lag time before such action is taken? Can employees access the organization’s information systems remotely? If so, is this privilege revoked immediately after termination of employment? Risk levels are one such dynamic, and as important in computer crime cases as they are in conventional crimes.
_1._Low Risk
Low-risk systems are small and generally are those that are not connected to the Internet. Not that such systems cannot be victimized, but rather the risk is lower because there will be a smaller number of threats from a limited number of insiders than from those who gain access via the Internet.
_2._Moderate Risk
Moderate-risk systems are those that, regardless of size or function, permit their staff to access the Internet and whose information security measures are cursory and unenforced or nonexistent (Boni and Kovavich 2000; Icove et al. 1995).
_3._High Risk
High-risk systems, large or small, are those that are connected to the Internet. Cutting off access to the Internet, however, does not, in and of itself, reduce vulnerability to attack. Some authorities believe that the trusted insider is a bigger threat than are “script kiddies” who are believed to constitute the vast majority of computer crackers.
B.Behavioral Assessment of the Crime Scene
An experienced investigator, while collecting the victim's background information, will also be alert for indicators that a crime scene can yield. Upon arrival at the scene, it is imperative that the investigator determines the scope of the scene and secures it. Serial killers have specific identifiable motives, although they may be hard to understand in the midst of an atypical crime scene. This is likely to be the case with regard to a serial cracker as well. Bizzare material is given great attention in the FBI profiling program.
If a pattern exists, even if not readily identifiable, a first responder should not be fooled by a change in expected modus operandi (MO). Some serial offenders will do this at the end of a spree to evade detection. It is likely that such behavior will become evident as cybercrimes become more pronounced. With violent offenses (murder, rape, bombings), many spree events cross several jurisdictional boundaries. This is almost always the case with serial computer crimes. Linkage blindness (Egger 1984) shouldn’t be allowed to cripple a computer crime investigation.
Multiagency task forces have been established in notorious or otherwise high-profile serial killer investigations, as in the Green River Killer case in the Pacific Northwest, for example (Keppel and Birnes 2003). This most certainly is an option worth planning for in the case of a serial computer criminal investigation.
_1._Victimology
Rape is an act of violence in which the offender uses sex as a way to express hostility, anger, and a desire for power and control. A rape victim has survived a potentially life-threatening situation. Things such as freedom of choice and decisions that control both mind and body have been stripped away. This type of traumatic event affects the victim greatly both physically and, more importantly, psychologically. A study conducted by Burgess and Holestrom (1979) analyzed 1600 victims of rape and determined that these victims had similar characteristics that are associated with post-traumatic stress disorder. The results of these interviews lead the researchers to coin the termrape trauma syndrome(Burgess and Holmstrom 1979). Victims ranging from diverse ethnic and socioeconomic backgrounds consistently described similar physical and emotional symptoms during, immediately following, and over a prolonged period of time after the rape. In 1980, the American Psychological Association incorporated rape trauma syndrome into its DSM-IV. Rape trauma syndrome was to be classified as a form of post-traumatic stress disorder. Rape and serial computer crime appear to have many parallels. At this early date in the development of empirical evidence in computer crime cases, it would appear to be useful for computer crime investigators and corporate information security staff to draw upon the rape investigation literature for pointers.
_2._Typology
Criminal justice academics Taylor and Loper (2003) as well as Carter and Katz-Bannister (2000) have done some fine preliminary work developing typologies building on theearlier work of Parker (1998). Classifying the serial computer criminal is crucial in determining the underlying motivating causal factors. Classification is made by assessing and analyzing the written, physical, and digital behaviors that exist in each attack. Interpreting the intrusion from the cracker’s point of view will greatly assist the investigator in understanding what motivates an offender. Four categories of rapists have been identified: power reassurance, power assertive, anger retaliatory, andsadistic (e.g., Lanning 1986; Hazelwood et al. 1987). Each category of rapist has a general group of prominent behavioral characteristics that enable the police to tailor the investigation to these specific actions. I believe this is possible with computercriminals as well. The investigator should be aware that just as the rapist’s behavior may become dynamic, so too will be the case with the cracker. These changes in behavior may require a reclassification of typology. The offenders’ MO may change over time with experience and egocentric thinking._Modus operandi_is defined as the actions taken by an offender to perpetrate the offense successfully (Ressler, Burgess, and Douglas 1988). This behavior will evolve, and successful outcomes will remain; whereas unsuccessful outcomes will be modified or eliminated. Essentially, crackers learn from their actions, and these results teach them what does and does not work. The offenders’ signature will be the common denominator that the police must identify for constructing an accurate profile._Signature_is defined as a repetitive ritualistic behavior that the offender usually displays at every crime scene (Ressler et al. 1988). Signature is overtly expressed through actions taken at the crime scene; these stem directlyfrom the offender’s fantasies. This action will give the investigators a clearer understanding of the mechanisms that drive this offender to commit these crimes. While investigating these offenses, the investigator should first analyze the attack independent of all others that seem to be related. After this is completed, characteristics may then be crossreferenced, identifying any common denominators. These findings will direct the investigators and assist in the classification of the type of offender thatis being sought.
VIII. Predictive Indicators
Both as individuals and as part of a research population, the behavioral traits of serial computer criminals will garner greater and greater interest from the research community. As these traits are studied,their importance in identifying serial computer criminals will become more and more important. A comprehensive index of traits of conventional serial offenders by Norris (1988) should be carefully evaluated for their applicability to serial computer criminals. In his offering Norris refers to such traits as_prediction indicators_and systematically defines the value of each. This formulation appears to be an important starting point for the construction of a system specifically applicable to serial computercriminals.
Space limitations preclude each item listed from being explained in depth here. However, this format may serve as a preliminary checklist. Knowledge of information like this can lead to the development of an instrument that will help professionals in identifying such traits in individuals, hopefully before they engage in intractable criminal activity. Practitioners in many areas of the criminal justice system should be made aware of these indicators, because an offender may come to the attention of different components of the criminal justice system at different times and, thus, to different practitioners in the system. I have modified the list of rapist indicators. This modified list includes most, but not all, of the indicators offered by Norris and others. It is believed the following apply to serial computer criminals in the making. The first professional to alert others in the system about an individual who displays an excessive number of these indicators could avert that person from becoming a full-blown serial computer criminal. A caveat is offered. Most teenagers go through a period of testing the limits of authority and harboring self-esteem concerns. Only in the extreme and chronic repetition of these traits are they viable indicators of a propensitytoward serial criminal behavior. In priority order, I believe these indicators are as follows:
Compulsiveness
Feelings of powerlessness or inadequacy
Excessive preference for solitary activity
Focus on a task at hand to the exclusion of everything else
Inability to control one’s temper
Inability to tell the truth
Inability to take responsibility for one’s own actions
Avoidance of age-appropriate responsibilities
Poor performance at school
Ritualistic behavior
Preoccupation with deviant sexual behavior/hypersexuality
Alcohol- or drug-abusing parents
Victim of physical or psychological abuse
Experimentation or abuse of drugs or alcohol
Unhappy childhood
Cruelty to animals
Fire setting
Bed wetting
History of serious head trauma
Injuries incurred at birth
Symptoms of neurological impairment
Evidence of genetic disorders
Biochemical imbalance
Severe memory disorders
Suicidal tendencies
IX.Methodology
Modus Operandi
Signature
Style of technical attack
Victimology
Content-driven
Text of message
Technical data specifics
Pattern recognition
Case dependent
Creatures of Habit
Repeat what works (MO)
Repeat what feels good (Sig)
Operate to the level of their abilities
Technique
Cadence
Rhythm
Keystroking pattern
Antidote of sysadmin of child porn IRQ
File-naming quirks
Linguistic and cultural markers
Stimuli elicits behavioral responses
Scientific evidence
X.Indicators of Further Positive Developments
It is appropriate to ask, what scientific evidence supports the contention that profiling will evolve and that serial computer criminals can be profiled? Three of the most promising recent developments that suggest this contention is viable are neurolinguistic analysis, neurotechnology research, and the intrusion prevention system Checkmate (Psynapse 2003).
A.Neurolinguistic Analysis
From his analysis ofPrimary Colors, published anonymously in 1996, English professor and the leading authority on attributional theory, Donald Foster (2000), concluded that this book was authored byNewsweek_columnist andCBS commentator Joe Klein. Klein denied the assertion, holding up Foster to ridicule. But Foster’s assessment was subsequently vindicated when Random House, the publisher of_Primary Colors, acknowledged Klein’s authorship. Computer scientist Peter Neumannhas observed, “RISKS readers are by now accustomed to being suspicious of purported computer evidence. Here, the winnowing out of Joe Klein’s identity by Professor Foster is in retrospect very impressive” (Neumann 1996). Also in the mid-1990s Dr. Foster was a consultant to the FBI on the Unabomber investigation. Foster’s work and further contributions to the literature on attributional theory can almost certainly be expected to shed considerable light on the ability to validly and reliably identify behavioral characteristics of serial computer criminals.
B.Neurotechnology Research
Since 1993 neuroscientists at the University of California at Los Angeles (UCLA) Brain Mapping Center have been using magnetic resonance imaging (MRI) technology to explore the landscape of the human brain. Its Director, John Mazziotta, believes that “the secrets of our thoughts and talents aren’t just hidden in dead cells under a microscope but in our own buzzing, rushing minds” (Kahn 2001, 109). The 10-year research efforts are aimed at building an omnidimensional, computerized database that synthesizes all the subspecialties of neurological research. Mazziotta further believes that “tiny aberrations drag us from normalcy into schizophrenia.” Brain mapping will surface the evidence (Kahn 2001, 108).
C.Checkmate
Based on behavioral theory and methodology, Washington, D.C.–based Psynapse Technologies (2003) has developed a state-of-the-art intrusion prevention system called Checkmate. This assessment engine tracks behavior to determine whether_intent_to inflict harm is present. When Checkmate detects a threat, it either blocks access automatically or provides an alert before damage occurs. The system detects new forms of attack unlike signature detection technologies that identify only known attacks for which rules have been incorporated in their program. Checkmate also recognizes when nontypical network activity is a genuine threat, which is distinguished from anomaly detection systems that only flag perfectly legitimate but unusualbehavior (Psynapse 2003).
XI.Insider Threat
A particularly thorny issue has to do with those instances in which a trusted insider is the offender. Insiders have unique knowledge that could forestall being identified or prosecuted even if identified. An outsider, no matter how carefully the cracker cases (i.e., surveillance prior to an attack) the target, there is always the opportunity to be detected. This threat is much less likely to result in exposure of the insider, who can more easily justify or explain away their activities.
XII.The Future ofCyberprofiling
Earlier it was noted that in the United States conventional profiling languishes under several disquieting issues. Four major and four lesser, but nevertheless important, credibility concerns are noted that should be addressed if CIBA is to avoid repeatinghistory. These must be resolved if the profiling of cyber offenders is to develop professional recognition and respect. First, individuals (civilian or sworn, employees or contractors), who assert expertise should be required to submit evidence of their qualifications and expertise to agencies that retain their services as profilers. Second, authentication should be established and easily available for verification. A certificate of subject-matter mastery — not simply attendance at seminars or other training programs — should be mandatory. Third, an academically accredited institution of higher learning should issue this certificate. Fourth, state licensing should be established. In addition, (a) a professional association should be established. One of itsfirst orders of business should be to set forth (b) a code of ethics. Next, (c) a certifying body, akin to the certified public accountant (CPA), professional engineer (PE), or the board certification of the American Medical Association (AMA) and the American Bar Association (ABA), should be established. Finally, (d) this association should establish a registry of its certified members.
Profiling is only one of several investigative tools. The average police officer and the typical detective may never encounter a serial offender — killer or cracker. Still, the use of profiling can assist in identifying, prioritizing, and even eliminating suspects in criminal cases committed by a serial computer criminal. The profiling technique attempts to paint a behavioralportrait of an offender in serial cases. This procedure is based on the premise that a digital crime scene reflects a pattern of behavior of a limited type of perpetrator who specializes in the commission of crime undertaken in a particular manner. Crimescene demeanor goes well beyond MO. This chapter is premised on the strong belief that a well-educated and properly trained computer crime investigator can develop the skills to recognize such patterns. Knowledge in the behavioral sciences (sociology, psychology, criminology, and criminal justice) will significantly aid in the investigation and identification of potential suspects that might otherwise be overlooked. Fusing the social sciences with the forensic sciences applied to the use of computer technology will be a tremendous asset to the future of what I have dubbed cyber investigative behavioral assessment (CIBA) — profiling.
Profiling will remain an important and increasingly used investigative tool throughout the Western world. It can reasonably beexpected that the results of rigorous academic research will refine and sharpen the process. The findings from replication and longitudinal studies will surely reduce threats to internal validity and mitigate reliability concerns.
Perhaps this tract will encourage others to contribute their own research to the literature by offering assessments as to the validity, reliability, and viability of this variation of conventional profiling. There is currently but a sliver of the body of knowledge of criminal investigation that concerns itself with helping investigators to recognize behavioral traits left at the scene of a crime. There is even less in the literature as it concerns serial computer criminals.
At a recent FBI Academy workshop, “Confronting the FutureChallenges of Cybercriminal Behavior Conference,” social scientist Max Kilger (2003) discussed his augmentation of a long-standing intelligence community concept, the acronym of which is MICE (money, ideology, compromise, and ego). Kilger’s variant is MEECES (money, entertainment, ego, cause or ideology, entrance to a social group, and status). The results of this undertaking by the FBI, as well as the important work of Kilger and his Project Honeynet colleagues are steps in the direction of a positive outcome.
References
Abel, G. G, and J. L. Rouleau. 1990. The Nature and Extent of Sexual Assault. InHandbook of Sexual Assault: Issues, Theories, and Treatment of the Offender, edited by D. R. Laws and H. E. Barbaree. New York: Plenum Press.
American Psychological Association (APA). 1998.Diagnostic and Statistical Manual of Mental Disorders (DSM-IV), 4th ed. (7th printing). Washington, D.C.: American Psychiatric Association.
Ault, R. L., and J. T. Reese. 1980. A Psychological Assessment of Crime Profiling._FB__I Law Enforcement Bulletin_49:3 (March): 22–25.
Boni, W., and G. L. Kovacich. 2000.Netspionage: The Global Threat to Information. Boston: Butterworth Heinemann.
Bruno, A. 1995.Seven. New York: St. Martin’s.
Bruno, A. 1993.The Iceman. New York: Dell.
Burgess, A. W., and L. L. Holmstrom. 1979.Rape: Crisis and Recovery. Bowie, MD: Robert J. Brady Publisher.
Cahill, T. 1987.Buried Dreams: Inside the Mind of a Serial Killer. New York: Bantam Books.
Canter, D. V., and L. J. Alison, eds. 1997.Criminal Det__ection and the Psychology of Crime. Brookfield, VT: Ashgate.
Carr, C. 1997.The Angel of Darkness. New York: Random House.
Carr, C. 1994.The Alientist. New York: Random House.
Carter, D. L., and A. J. (Katz) Bannister. 2000. Computer Crime: A Forecast ofEmerging Trends. An Independent Research Project Report, School of Criminal Justice, Michigan State University.
Casey, E. 2000.Digital Evidence and Computer Crime. San Diego: Academic Press. See esp. Using Digital Evidence and Behavioral Evidence Analysisin an Investigation, 161–170.
Casey, E. 1999. Cyberpatterns: Criminal Behavior on the Internet. InCriminal Profiling: An Introduction to Behavioral Evidence Analysis, by B. Turvey. London: Academic Press.
Copson, G. 1995. Coals to Newcastle? Part 1: A Study of Offender Profiling. Paper 7. London, England: Police Research Group Special Interest Series, Home Office.
Dietz, P. E., R. R. Hazelwood, and J. Warren. 1990. The Sexually Sadistic Criminal and His Offenses._Bulletin of the American Academy of Psychi__atry & Law_18: 163–178.
Douglas, J. E. and M. Olshaker. 1998.Obsession. New York: Scribner.
Douglas, J. E., and M. Olshaker. 1997.Journey into Darkness. New York: Scribner.
Douglas, J. E. and M. Olshaker. 1996.Unabomber. New York: Pocket Books.
Douglas, J. E., and M. Olshaker. 1995.Mind Hunter. New York: Scribner.
Douglas, J. E., A. W. Burgess, A. G. Burgess, and R. K. Ressler. 1992.Crime Classification Manual. Lexington MA: Lexington Books.
Douglas, J. E., R. K. Ressler, A. W. Burgess, and C.R. Hartman. 1986. Criminal Profiling from Crime Scene Analysis._Behavioral Sciences & the Law_4: 401–421.
Edmond, B. and R. L. West. 2003. Cyberpsychology: A Human-Interaction Perspective Based on Cognitive Modeling._Journal of Cyberpsychology and Behavior_6:5 (October): 527–536.
Egger, S. A. 1990.Serial Murder: An Elusive Phenomenon. New York: Praeger.
Egger, S. A. 1998.The Killers Among Us. Saddle River, NJ: Prentice Hall.
Egger, S. A. 1984. A Working Definition of Serial Murder and the Reduction of Linkage Blindness.Journal of Police Science and Administration, 12: 348–357.
Feshbach, S., and J. Zagrodzka, eds. 1998.Aggression: Biological, Developmental, and Social Perspectives. New York: Plenum Publishing.
Foster, D. W. 2000.Author Anonymous. New York: Henry Holt and Co.
Geberth, V. J. 1990.Practical Homicide Investigation, 2nd ed. New York: Elsevier.
Geberth, V. J. 1981. Psychological Profiling._Law and Order_29(September): 46–52.
Graysmith, R. 1997.Unabomber: A Desire to Kill. Washington,D.C.: Regnery Publishing.
Greenfield, D. N. 1999. Psychological Characteristics of Compulsive Internet Use: A Preliminary Analysis._Journal of Cyberpsychology and Behavior_2:5 (September).
Gudaitis, T. 2001. The Human Side of Incident Response. InInciden__t Response: A Strategic Guide to Handling System and Network Security Breaches, by E. E. Schultz and R. Shumay. Upper Saddle River, NJ: Pearson, 207–246.
Gudaitis, T. 2000. Cybercrime and the Hidden Aspects of Incident Response._Information Security Bullet__in_5: 3 (April): 15–24.
Hazelwood, R. R. 2004. Personal conversation with the author by telephone January 29th.
Hazelwood, R. R. 1986. NCAVC Training Program: A Commitment to Law Enforcement._FBI Law Enforcement Bulletin_55:12(December).
Hazelwood, R. R. 1983. The Behavior-Orientated Interview of Rape Victims: The Key to Profiling._FBI Law Enforcement Bulletin_52:9 (September): 8–15.
Hazelwood, R. R., and A. W. Burgess, eds. 2004.Practical Aspects of Rape Investigation: A Multidisciplinary Approach, 4th ed. New York: Elsevier.
Hazelwood, R. R., and A. W. Burgess. 1989. The Serial Rapist: His Characteristics and Victims._FBI Law Enforcement Bulletin_58:2 (February): 18–25.
Hazelwood, R. R., and A. W. Burgess. 1987. An Introduction to the Serial Rapist._FBI L__aw Enforcement Bulletin_56:9 (September): 16–24.
Hazelwood, R. R., and A. W. Burgess, eds. 1987.Practical Aspects of Rape Investigation: A Multidisciplinary Approach. New York: Elsevier.
Hazelwood, R. R., and J. E. Douglas. 1980. The Lust Murderer._FBI La__w Enforcement Bulletin_49:4 (April): 18–22.
Hazelwood, R. R., and J. Warren. 1990. The Criminal Behavior of the Serial Rapist._FBI Law Enforcement Bulletin_60:2 (February): 11–16.
Hazelwood, R. R., and J. Warren. 1989. The Serial Rapist: Characteristics and Victims._FBI Law Enforcement Bulletin_58:1 (January): 10–17.
Hazelwood, R. R., P. E. Dietz, and A. W. Burgess. 1983.Autoerotic Fatalities. Lexington, MA: Lexington Books.
Hazelwood, R. R., R. K. Ressler, R. L. Depue, and J. E. Douglas. 1987. Criminal Personality Profiling: An Overview. InPractical Aspects of Rape Investigation: A Multidisciplinary Approach, edited by R. R. Hazelwood and A. W. Burgess. New York: Elsevier, 137–149.
Hazelwood, R. R., et al. 1982. Sexual Fatalities: Behavioral Reconstruction in Equivocal Deaths._Journal of Forensic Science_27:4 (October): 764–773.
Hickey, E. W. 1991.Serial Murderers and Their Victims. Belmont, CA: Wadsworth.
Hollinger, R. 1988. Computer Hackers Follow a Guttman-like Progression._Social Science Review_72:199–200.
Howlett, J. B., K. A. Hanfland, and R. K. Ressler. 1986. The Violent Criminal Apprehension Program — VICAP: A Progress Report._FBI Law Enforcement Bulletin_55:14–22.
Hudson, R. A. 1999.Who Becomes a Terrorist and Why: The 1999 Government Report on Profiling Terrorists. Guilford, CT: Lyons Press.
Hunter, J. A. 2001. The Sexual Crimes of Juveniles. InPractical Aspects of Rape Investigation: A Multidisciplinary Approach, 3rd ed., edited by R. R. Hazelwood and A. W. Burgess. New York: Elsevier, 409.
Icove, D. J. 1986. Automated Crime Profiling._FBI Law Enforcement Bulletin_55:12(December).
Icove, D. J., K. Seger, and W. VonStorch. 1995.Computer Crime: A Crimefighter’s Ha__ndbook. Sebastopol, CA: O’Reilly and Associates.
Icove, D. J., V. B. Wherry, and J. D. Schroeder. 1998.Combating Arson-for-Profit: Advanced Techniques for Investigators, 2nd ed. Columbus, OH: Battelle. See esp. 51–55.
Jackson, J. L., and D. A. Bekerian, eds. 1997.Offender Profiling: Theory, Research and Practice. Chichester, UK: John Wiley and Sons.
Jarvis, J. P. 2003. Confronting the Future Challenges of Cybercriminal Behavior Conference, FBI Academy, Quantico, VA (August 18–22).
Kahn, Jennifer. 2001. Let’s Make Your Head Interactive.Wired_9: 8 (August): 106–115. Kelleher, M. D. 1997._Flash Point: The American Mass Murderer. Westport, CT: Praeger.
Kelsoe, P. L. 1996._Criminal Investigative Analysis Quarterly Newsletter_1:1(September) Corona, CA: Pique Publising.
Keppel, R. D. 1989.Serial Murder: Future Implications for Police Investigators. Cincinnati, OH: Anderson.
Keppel, R. D., and W. J. Birnes. 2003.The Psychology of Serial Killer Investigations. San Diego, CA: Academic Press.
Kilger, M. 2003. Exchange with the author at the workshop, Confronting the Future Challenges of Cybercriminal Behavior Conference, at the FBI Academy, Quantico, VA (August 21).
Kilger, M., O. Arkin, and J. Stutzman. 2002. Profiling. InKnow Your Enemy, by Honeynet Project. Reading, MA: Addison-Wesley.
Kruse, W. G., II, and J. G. Heiser. 2002.Computer Forensics: Incident Response Essentials. Boston: Addison-Wesley.
Kuhn, T. S. 1996.The Structure of Scientific Revolutions, 3rd ed. Chicago: University of Chicago Press.
Lanning, K. V. 1986. Child Molesters: A Behavioral Analysis.Monograph, Washington, D.C.: National Center for Missing & Exploited Children.
Levin, J., and J. A. Fox. 1985.Mass Murder. New York: Plenum Publishing.
Levy, Steven. 1984.Hackers: Heroes of the Computer Revolution. New York: Doubleday.
Levy, S., 1984.Hackers: Heroes of the Computer Revolution. Garden City, NY: Anchor Press.
Lundgren, D. C. 1997. Conceptualizing Serial Murder: A Sociological Critique of the Psychological Paradigm. unpublished Paper, Board of Studies in Sociology, Stevenson College, University of California, Santa Cruz.
Marshall, W. L., et al, eds. 1998.Sourcebook of Treatment Programs for Sexual Offenders. New York: Plenum Publishing.
Michaud, S. C. 1986. The FBIs New Psyche Squad.New York Times Magazine(October 26):40, 42, 50, 74, and 76–77.
Monahan, L. 2003. Criminal Justice Faculty Meeting, University of New Haven, May 2. Norris, J. 1988.Serial Killers: The Growing Menace. New York: Doubleday.
Osterburg, J. W., and R. H. Ward. 1997.Criminal Investigation, 2nd ed. Cincinnati, OH: Anderson. See esp. 150–153.
Parker, D. B. 1998.Fighting Computer Crime. New York: John Wiley & Sons.
PBS. 1992. Mind of a Serial Killer. Nova TelevisionPublic Broadcasting System, Program #1912 (October 18).
Pinnizzotto, A. J. 1984. Forensic Psychology: Criminal Personality Profiling._Journal of Police Science and Administration_12(1):32–36.
Project Honeynet. 2002.Know Your Enemy. Reading, MA: Addison-Wesley. See esp. Profiling Review, 260–26,1 and Psychological Review, 262–264.
Reboussin, R. 1990. An Expert System Designed to Profile Murderers. InComputers in Criminal Justice; Issues & Applications, edited by Schmalleger, F. Bristol, IN: Wyndham Hall Press, 237–243.
Ressler, R. K., ed. 1985. Violent Crimes._FBI Law Enforcement Bulletin_54:1–3.
Ressler, R. K., and A. W. Burgess. 1985. The Split Reality of Murder._FBI Law Enforcement Bulletin_54:7–11.
Ressler, R. K., and T. Shachtman. 1998. I Have Lived inthe Monster: Inside the Minds of the World’s Most Notorious Serial Killers. New York: St. Martin’s.
Ressler, R. K., and T. Shachtman. 1994. Whoever Fights Monsters. New York: St. Martin’s.
Ressler, R. K., A. W. Burgess, and J. E. Douglas. 1988. Sexual Homicide: Patterns and Motives. Lexington, MA: Lexington Books.
Ressler, R. K., A. W. Burgess, J. E. Douglas, and R. L. Depue. 1985. Criminal Profiling Research in Homicide. In Rape and Sexual Assault: A Research Handbook, edited by A. W. Burgess. New York: Garland, 343–349.
Ressler, R. K., A. W. Burgess, J. E. Douglas, and A. McCormack. 1986. Murderers Who Rape & Mutilate. Journal of Interpersonal Violence 1:3: 273–287.
Ressler, R. K., et al. 1980. Offender Profiles: A Multidisciplinary Approach. FBI Law Enforcement Bulletin 49:9 (September): 16–20.
Ross, D. 1998._Looking into the Eyes of a Killer._New York: Plenum Publishing.
Rossmo, D. K. 1998. Geographic Profiling. Presentation at the annual conference of the National Criminal Intelligence Service, the Henry Fielding Centre for Police Studies and Crime Risk Management, University of Manchester (March 18), Manchester, England.
Rossmo, D. K. 1996. Targeting Victims: Serial Killers and the Urban Enviroment. In_Serial and Mass Murder: Theory, Research, and Polic__y,_edited by T. O’Reily-Fleming. Toronto: Canadian Scholars Press.
Samenow, S. E. 1984._Inside the Criminal Mind._New York: Times Books.
Shimomura, T., with J. Markoff. 1996._Take-Down._New York: Hyperion.
Stoll, C. 1989._The Cuckoo’s Egg: Tracking a Spy through the Maze of Computer Espionage._New York: Doubleday.
Strentz, T. 1988. A Terrorist Psychosocial Profile: Past and Present. FBI Law Enforcement Bulletin, 57: 4: 11–18.
Strentz, T. 1981. The Terrorist Organizational Profile: A Psychological Role Model. In_Behavioral and Quantitative Perspectives on Terrorism,_edited by Y. Alexander and J. M. Gleason. New York: Pergamon Press.
Swanson, C. R., N. C. Chamelin, and L. Territo. 1984._Criminal Investigation._New York: Random House.
Tafoya, W. L. 2003. The CyberPsychology of Serial Cyber Offenders. Colloquium,
Cyberpsychology Institute, Brandeis University (November 18), Waltham,
MA.
Tafoya, W. L. 2001. Wetware Whacking: Profiling the Computer Hacker. Keynote Address, Defcon 9 Conference (July 13) Las Vegas, NV.
Tafoya, W. L. 1998. Offender Profiling. National Criminal Intelligence Service Conference, the Henry Fielding Centre for Police Studies and Crime Risk Management, University of Manchester (March 18), Manchester, England.
Tafoya, W. L., and T. M. Gudaitis. 2003. Profiling the Computer Intruder. Computer Security Institute Conference (November 3) Washington, D.C.
Taylor, R. W., and D. K. Loper. 2003. Computer Crime. InCrimin__al Investigation, 8th ed., by C. R. Swanson, et al. Boson: McGraw Hill, 584–625. See esp. The Hacker Profile and The Computer Criminal Profile, 610–613.
Thieme, R. 2001. Profile of a Profiler._Information Security_4:4 (April): 90–96 (Interview of William L. Tafoya).
Thomas, D., and B. D. Loader. 2000.Cybercrime: Law Enforcement, Security and Surveillance in the Information Age. London: Routledge.
Turco, R. 1998.Closely Watched Shadows: A Profile of the Hunted and the Hunter. Bookpartners.
Van Hasselt, V.B., and M. Hersen, eds. 1998.Handbook of Psychological Approaches with Violent Offenders. New York: Plenum Publishing.
Vorpagel, R. 1998.Profiles in Murder. New York: Plenum Publishing.
Waxman, H. S. 2003. Interview, Cyberpsychology Institute, Brandeis University (November 18) Waltham, MA.
Yochelson, S., and S. E. Samenow. 1976.The Criminal Personality, 3 vol. New York: Jason Aronson.
Web Sources
CSC. 2002. How CSC’s Bill Tafoya Applies Creative Thinking to IT Security. Office of Homeland Security, Computer Sciences Corporation, Falls Church, VA. Online at: http://www.csc.com/features/2002/17.shtml.
Golubev, V. 2003. Criminalistic Characteristics of Cybercrimes’ Committees. Online at: http://www.crime-research.org/eng/library/Golubev.mar.html.
Hulme, George V. 2003. The Mind of a Hacker.Information Week. Online at: www.informationweek.com/story/showArticle.jhtml?articleID=16000606.
Interpol European Working Group on Information Technology Crime. 2002. White Hat v. Black Hat. SC Infosec Opinionwire. Online at: http://www.infosecnews. com/opinion/2002/12/11_01.htm.
Journal of Cyberpsychology and Behavior. Online at: http://www.liebertpub.com/ pagedisplay/Toc.asp?id=10.
Karnov, C., R. Landels, and D. Landels. 1994. Recombinant Culture: Crime in the Digital Network. Online at: http://www.cpsr.org/privacy.
Kilger, M. 2000. Determining When Something Is NOT Random. The Smoo Group IDS (July 25). Online at:http://www.shmoo.com/mail/ids/jul00/ msg00135.shtml.
Langer, W. C., et al. 1943. A Psychological Analysis of Adolph Hitler: His Life and Legend. Report Prepared for the Office of Strategic Services, Washington, D.C. Online at: http://www1.ca.nizkor.org/hweb/people/h/hitler-adolf/ oss-papers/text/profile-index.html.
Lemos, R. 2004. MyDoom Variant Targets Microsoft.New York Times(January 28). Online at: http://www.nytimes.com/cnet/CNET_2100-7355_
3-5149504.html.
LSU. 2003. Research on the Profiling Problemin Cybersecurity and Anti-Terrorism. Peter P. Chen, Principal Investigator, Louisiana State University. Online at:
http://www.lsu.edu/ncsrt/ncsrt/ncsrt_cybersecurity.htm.
Neumann, P. G. 1996. The RISKS Digest. 18:26 (July 19). Online at: http://catless. ncl.ac.uk/Risks/18.26.html#subj1.
Neurotechnology Research, Brain Mapping Center, University of California at Los Angeles. Online at: http://www.neurology.ucla.edu/brainmap.htm.
Psynapse Technologies. 2003. Checkmate. Intrusion Prevention System. Online at:http://www.psynapse.com.
Rogers, M. 1999. Psychology of Hackers: Steps Toward a New Taxonomy. Online at:
Roy, G. nd. Plot Summary for Blade Runner (1982). Online at: http://www.imdb. com/title/tt0083658/plotsummary.
Saita, A. 2001. Hacker Psychology. Information Security (June). Online at:
http://infosecuritymag.techtarget.com/articles/june01/features_hacker_ psychology.shtml.
Scripps-Howard. 1996. How David Kaczynski Came to Realize Brother Might Be Unabomber. Sacbee. Online at: http://www.unabombertrial.com/archive/ 1996/041096-4.html.
Thieme, R. 2001. Profile of a Profiler._Information Security_4:4(April): 90–96. Online at: http://infosecuritymag.techtarget.com/articles/april01/features_q&a.shtml.
Verton, D. 2001. Analysis: Insiders a Major Security Threat. CNN.com. Online at: http://www.cnn.com/2001/TECH/industry/07/11/insider.threat.idg/?related.
Witkin, G. 1997. Did the FBI Ignore the “Tafoya Profile”?U. S. News &World Report(November 17): 24. Online at: http://www.usnews.com/usnews/issue/97117/ 17unab.htp.
Acknowledgements
Appreciation is expressed for the invaluable contributions of Max Kilger, Terry Gudaitis, and David J. Icove for their ideas, suggestions, and inspiration with respect to the assessment of the behavior of computer abusers. Thanks are also owed to Mark Brenzinger and Wayne A. Johnson for their input in the collaboration of an earlier albeit unpublished effort, the focus of which was the articulation of noncomputer crime profiling.
Investigative Strategy